Internet Group Management Protocol
View on Wikipedia| Internet protocol suite |
|---|
| Application layer |
| Transport layer |
| Internet layer |
| Link layer |
The Internet Group Management Protocol (IGMP) is a communications protocol used by hosts and adjacent routers on IPv4 networks to establish multicast group memberships. IGMP is an integral part of IP multicast and allows the network to direct multicast transmissions only to hosts that have requested them.
IGMP can be used for one-to-many networking applications such as online streaming video and gaming, and allows more efficient use of resources when supporting these types of applications.
IGMP is used on IPv4 networks. Multicast management on IPv6 networks is handled by Multicast Listener Discovery (MLD) which is a part of ICMPv6 in contrast to IGMP's bare IP encapsulation.
Architecture
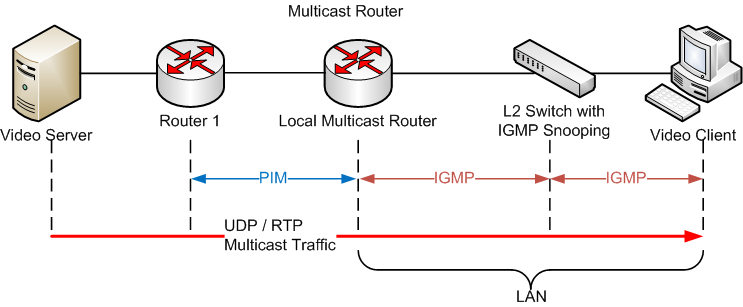
[edit]A network designed to deliver a multicast service using IGMP might use this basic architecture:
IGMP operates between a host and a local multicast router. Switches featuring IGMP snooping also derive useful information by observing these IGMP transactions. Protocol Independent Multicast (PIM) is then used between the local and remote multicast routers to direct multicast traffic from hosts sending multicasts to hosts that have registered through IGMP to receive them.
IGMP operates on the network layer (layer 3), just the same as other network management protocols like ICMP.[1]
The IGMP protocol is implemented on hosts and within routers. A host requests membership to a group through its local router while a router listens for these requests and periodically sends out subscription queries. A single router per subnet is elected to perform this querying function. Some multilayer switches include an IGMP querier capability to allow their IGMP snooping features to work in the absence of an IGMP-capable router in the layer 2 network.
IGMP is vulnerable to some attacks,[2][3][4][5] and firewalls commonly allow the user to disable it if not needed.
Versions
[edit]There are three versions of IGMP.[6] IGMPv1 was defined in 1989.[7] IGMPv2, defined in 1997,[8] improves IGMPv1 by adding the ability for a host to signal a desire to leave a multicast group.
In 2002, IGMPv3 improved IGMPv2 by supporting source-specific multicast[9] and introduces membership report aggregation.[10] The support for source-specific multicast was improved in 2006.[11]
The three versions of IGMP are backward compatible. A router supporting IGMPv3 can support clients running IGMPv1, IGMPv2, and IGMPv3. IGMPv1 uses a query-response model. Queries are sent to 224.0.0.1. Membership reports are sent to the group's multicast address. IGMPv2 accelerates the process of leaving a group and adjusts other timeouts. Leave-group messages are sent to 224.0.0.2. A group-specific query is introduced. Group-specific queries are sent to the group's multicast address. A means for routers to select an IGMP querier for the network is introduced. IGMPv3 introduces source-specific multicast capability. Membership reports are sent to 224.0.0.22.
Messages
[edit]There are several types of IGMP messages:
- General membership queries
- Sent by multicast routers to determine which multicast addresses are of interest to systems attached to the network(s) they serve to refresh the group membership state for all systems on its network.
- Group-specific membership queries
- Used for determining the reception state for a particular multicast address.
- Group-and-source-specific queries
- Allow the router to determine if any systems desire reception of messages sent to a multicast group from a source address specified in a list of unicast addresses.
- Membership reports
- Sent by multicast receivers in response to a membership query or asynchronously when first registering for a multicast group.
- Leave group messages
- Sent by multicast receivers when specified multicast transmissions are no longer needed at the receiver.
IGMP messages are carried in bare IP packets with IP protocol number 2.[10]: §4 Similar to the Internet Control Message Protocol, there is no transport layer used with IGMP messaging.
IGMPv2 messages
[edit]| Offset | Octet | 0 | 1 | 2 | 3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Octet | Bit | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 | 21 | 22 | 23 | 24 | 25 | 26 | 27 | 28 | 29 | 30 | 31 |
| 0 | 0 | Type | Maximum Response Time | Checksum | |||||||||||||||||||||||||||||
| 4 | 32 | Group Address | |||||||||||||||||||||||||||||||
- Type: 8 bits
- Indicates the message type as follows:
Message Type value Membership Query 0x11 IGMPv1 Membership Report 0x12 IGMPv2 Membership Report 0x16 IGMPv3 Membership Report 0x22 Leave Group 0x17
- Maximum Response Time: 8 bits
- Specifies the required responsiveness of replies to a Membership Query (0x11). This field is meaningful only in Membership Query; in other messages, it is set to 0 and ignored by the receiver. The field specifies time in units of 0.1 second (a field value of 10 specifies 1 second). Larger values reduce IGMP traffic burstiness and smaller values improve protocol responsiveness when the last host leaves a group.[8]: §2.2
- Checksum: 16 bits
- This is the 16-bit ones' complement of the ones' complement sum of the entire IGMP message. Computed before sending, with this field set to zero. When re-computed on reception of the packet, this field is included, and the result should be zero.
- Group Address: 32 bits
- This is the multicast address being queried when sending a Group-Specific or Group-and-Source-Specific Query. The field is zeroed when sending a General Query.
- The message is sent to the following IP multicast addresses:[8]: §9
Message type Multicast address General Query All hosts (224.0.0.1) Group-Specific Query The group being queried Membership Report (all IGMP versions) The group being reported Leave Group All routers (224.0.0.2)
IGMPv3 membership query
[edit]| Offset | Octet | 0 | 1 | 2 | 3 | ||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Octet | Bit | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 | 21 | 22 | 23 | 24 | 25 | 26 | 27 | 28 | 29 | 30 | 31 |
| 0 | 0 | Type (0x11) | Maximum Response Code | Checksum | |||||||||||||||||||||||||||||
| 4 | 32 | Group Address | |||||||||||||||||||||||||||||||
| 8 | 64 | Reserved | S | QRV | QQIC | Number of Sources (N) | |||||||||||||||||||||||||||
| 12 | 96 | Source Address[1] | |||||||||||||||||||||||||||||||
| 16 | 128 | Source Address[2] | |||||||||||||||||||||||||||||||
| ⋮ | ⋮ | ⋮ | |||||||||||||||||||||||||||||||
| | | Source Address[n] | |||||||||||||||||||||||||||||||
- Type: 8 bits
- Indicates the type of the packet. A value of 0x11 indicates IGMPv3 Membership Query.
- Maximum Response Code: 8 bits
- This field is used to compute the Maximum Response Time (in 1/10 second increments) allowed before sending a responding report. If the number is below 128, the value is used directly. If the value is 128 or more, it is interpreted as an exponent and mantissa.
- Checksum: 16 bits
- This is the 16-bit ones' complement of the ones' complement sum of the entire IGMP message. Computed before sending, with this field set to zero. When re-computed on reception of the packet, this field is included, and the result should be zero.
- Group Address: 32 bits
- This is the multicast address being queried when sending a Group-Specific or Group-and-Source-Specific Query. The field is zeroed when sending a General Query.
- Reserved: 4 bits
- This field is reserved. It should be zeroed when sent and ignored when received.
- Suppress Router-side Processing (S): 1 bit
- When this flag is set, it indicates to receiving routers that they are to suppress the normal timer updates.
- Querier's Robustness Variable (QRV): 3 bits
- If this is non-zero, it contains the Robustness Variable value used by the sender of the query. Routers should update their Robustness Variable to match the most recently received query unless the value is zero. QRV sets tolerance for packet loss, allowing up to QRV - 1 lost packets. Zero is invalid, one is discouraged; default is 2.
- Querier's Query Interval Code (QQIC): 8 bits
- This code is used to specify the Query Interval value (in seconds) used by the querier. If the number is below 128, the value is used directly. If the value is 128 or more, it is interpreted as an exponent and mantissa.
- Number of Sources (N): 16 bits
- This field specifies the number of source addresses present in the query. For General and Group-Specific Queries, this value is zero. For Group-and-Source-Specific Queries, this value is non-zero, but limited by the network's MTU.
- Source Address [i]: 32 bits
- The Source Address [i] fields are a vector of n IP unicast addresses, where n is the value in the Number of Sources (N) field.
Implementations
[edit]See also
[edit]Notes
[edit]References
[edit]- ^ Forouzan, Behrouz A. (2012). Data Communications and Networking (5th ed.). New York, NY: McGraw-Hill. p. 658. ISBN 978-0073376226.
- ^ Spoofed IGMP report denial of service vulnerability.
- ^ "Fragmented IGMP Packet May Promote "Denial of Service" Attack". Dec 20, 2004. Archived from the original on 2005-02-13.
- ^ IGMP Security Problem Statement and Requirements Archived 2006-10-13 at the Wayback Machine.
- ^ "Vulnerability in TCP/IP Could Allow Denial of Service (MS06-007, 913446))". Microsoft. February 14, 2006. Archived from the original on 2007-02-05.
- ^ IP Multicast Routing Configuration Guide, Cisco, pp. 25–28, retrieved 2017-05-27
- ^ S. Deering (August 1989). Host Extensions for IP Multicasting. Network Working Group. doi:10.17487/RFC1112. STD 5. RFC 1112. Internet Standard 5. Obsoletes RFC 988 and 1054. Updated by RFC 2236.
- ^ a b c d W. Fenner (November 1997). Internet Group Management Protocol, Version 2. Network Working Group. doi:10.17487/RFC2236. RFC 2236. Proposed Standard. Updates RFC 1112. Updated by RFC 3376 and 9776.
- ^ "Internet Group Management Protocol Overview". Javvin. Archived from the original on 2010-11-10. Retrieved 2010-11-18.
- ^ a b c B. Cain; S. Deering; I. Kouvelas; B. Fenner; A. Thyagarajan (October 2002). Internet Group Management Protocol, Version 3. Network Working Group. doi:10.17487/RFC3376. RFC 3376. Obsolete. Obsoleted by RFC 9776. Updates RFC 2236. Updated by RFC 4604.
- ^ H. Holbrook; B. Cain; B. Haberman (August 2006). Using Internet Group Management Protocol Version 3 (IGMPv3) and Multicast Listener Discovery Protocol Version 2 (MLDv2) for Source-Specific Multicast. Network Working Group. doi:10.17487/RFC4604. RFC 4604. Proposed Standard. Updates RFC 3376 and 3810.
Internet Group Management Protocol
View on GrokipediaIntroduction
Purpose and Functionality
The Internet Group Management Protocol (IGMP) is a communications protocol used by hosts and adjacent routers on IPv4 networks to establish and maintain multicast group memberships.[1] IGMP enables hosts to inform routers about their interest in receiving traffic destined for specific IP multicast addresses, allowing routers to forward multicast packets only to subnets with interested receivers rather than flooding the entire network.[2] This mechanism supports efficient one-to-many and many-to-many communications, conserving bandwidth in applications such as IPTV, online gaming, video conferencing, and collaborative tools where multiple recipients need simultaneous data delivery.[4][5] IGMP operates exclusively at the link-local scope, facilitating communications between hosts and routers on the same subnet without propagating messages across routers.[1] It is assigned IP protocol number 2 in the IPv4 header, positioning it at the network layer (OSI Layer 3) to manage multicast routing decisions. IGMP specifically handles memberships for IPv4 multicast addresses in the Class D range, from 224.0.0.0 to 239.255.255.255, which are reserved for group communications. Later versions, such as IGMPv3, extend support to source-specific multicast, allowing hosts to filter traffic from specific sources.[2] By limiting multicast traffic to interested parties, IGMP reduces network congestion and enhances scalability for real-time data distribution.[2]Historical Development
The development of the Internet Group Management Protocol (IGMP) originated from early research on IP multicast at Stanford University in the mid-1980s, led by Steve Deering, who explored multicast routing mechanisms to enable efficient group communication in datagram internetworks. This work built on experiments with multicast addressing and routing in ARPANET environments during the late 1980s, aiming to extend IP capabilities beyond unicast for applications like distributed computing and video conferencing.[2] Deering's efforts culminated in the initial standardization of IGMP as part of the host extensions for IP multicasting, defined in RFC 1112 in August 1989, which introduced IGMPv1 to allow hosts to report multicast group memberships to adjacent routers.[2] Subsequent evolution addressed limitations in group management efficiency, with IGMPv2 specified in RFC 2236 in November 1997 by William C. Fenner, updating RFC 1112 to include mechanisms for faster group leave notifications and improved query handling.[3] This version emerged from the IETF's Inter-Domain Multicast Routing Working Group, reflecting growing needs for scalable multicast in expanding internetworks. By the mid-1990s, IGMP had seen widespread adoption in Unix-based systems, including BSD variants, integrating into kernel-level support for multicast applications and becoming a standard component of IP networking stacks.[3] Further advancements came with IGMPv3 in RFC 3376, published in October 2002 by a team including Deering and Fenner, which obsoleted RFC 2236 and added support for source-specific multicast to enable finer-grained control over multicast traffic.[1] This specification was refined in 2006 through RFC 4604 by Holbrook, Cain, and Haberman, which clarified IGMPv3 behaviors for source-specific multicast implementations, ensuring better interoperability in diverse network environments.[6] IGMPv3 was further updated in RFC 9776 in March 2025 to address errata and provide clarifications while maintaining backward compatibility.[1] IGMP's integration into IETF standards track documents solidified its role in IPv4 multicast, as focus shifted toward IPv6 equivalents like Multicast Listener Discovery (MLD).[7]Architecture
Roles of Hosts and Routers
In the Internet Group Management Protocol (IGMP), hosts and routers play distinct roles in managing multicast group memberships on local networks. Hosts are responsible for reporting their interest in receiving multicast traffic for specific groups, while routers act as queriers to solicit and process these reports to determine which multicast traffic to forward onto the local segment.[2][3][1] Hosts initiate group membership by sending unsolicited membership reports upon joining a multicast group, announcing their interest to all routers on the local network; these reports are typically transmitted immediately and may be repeated 1-2 times with short intervals to ensure reception. When a router sends a query, hosts respond with membership reports after a random delay to prevent message implosion, suppressing their own report if they detect another host's report for the same group during the delay period. In IGMP versions 2 and later, hosts that are the last reporter for a group send a leave message upon departing to promptly notify routers, reducing unnecessary traffic forwarding. Hosts also maintain internal timers for report suppression and group membership states to optimize local communications.[2][3][1] Multicast routers, particularly the elected querier, periodically send general queries to all hosts on the attached network to discover and refresh group memberships, using the all-systems multicast address 224.0.0.1 with a time-to-live (TTL) of 1 to limit scope to the local link. The querier processes incoming reports to update its forwarding tables, enabling efficient multicast distribution based on active group interests. On local area networks (LANs) with multiple routers, a querier election occurs, where the router with the lowest IP address assumes the querier role, and others become non-queriers that passively listen for reports and queries without initiating them. Non-querier routers adjust their timers upon detecting a querier but do not send queries or leave messages. These roles operate in an all-senders-to-all-receivers model on shared LANs, where IGMP messages are link-local and processed by all participants.[2][3][1] IGMP employs several foundational timer mechanisms to manage membership states reliably: the Query Interval (QI) governs the periodicity of general queries from the querier; the Query Response Interval (QRI) sets the maximum time hosts wait before responding to queries; and the Group Membership Interval (GMI) defines the duration after which a router assumes a group has no members if no reports are received, typically derived as (Robustness Variable × QI) + QRI. These timers help mitigate packet loss and ensure timely updates to multicast forwarding.[3][1] The roles defined in IGMP integrate with multicast routing protocols such as Protocol Independent Multicast (PIM), where routers use IGMP reports to inform tree-building decisions for wider network distribution.[8]Interaction with Other Protocols
IGMP operates as an integral component of the IPv4 multicast framework, with its messages encapsulated directly within IPv4 datagrams using the IP protocol number 2. This encapsulation ensures that IGMP communications are treated as a distinct protocol layer atop IP, facilitating the exchange of group membership information between hosts and routers on the same local network segment. Additionally, all IGMP messages are transmitted with an IP Time-to-Live (TTL) value of 1, restricting their scope to the local link and preventing unintended propagation beyond the immediate subnet.[9][1] IGMP integrates closely with multicast routing protocols by supplying edge-network information on host group memberships, enabling routers to construct and maintain efficient multicast distribution trees across the wider network. For instance, in Protocol Independent Multicast (PIM), IGMP reports inform routers about local receiver interests, allowing PIM to build shared or source-specific trees that direct traffic only to subnets with active members, thereby optimizing bandwidth usage. Similarly, the Distance Vector Multicast Routing Protocol (DVMRP) relies on IGMP queries and reports to track local group memberships, using this data to propagate route advertisements and prune unnecessary branches in the multicast forwarding tree.[1][10] At the Layer 2 level, IGMP interacts with switch mechanisms such as IGMP snooping, where Ethernet switches monitor IGMP messages to dynamically build port-based membership tables, forwarding multicast traffic only to ports associated with interested hosts rather than flooding all ports. This optimization reduces unnecessary traffic replication, conserves bandwidth, and mitigates the risk of broadcast storms in environments with high multicast activity.[11] For IPv6 networks, IGMP's functionality is mirrored by Multicast Listener Discovery (MLD), an ICMPv6-based protocol that performs analogous group membership reporting but uses distinct message types, such as Multicast Listener Query (type 130) and Report (type 131). MLD versions align with IGMP's evolution—MLDv1 corresponds to IGMPv2, while MLDv2 supports source-specific filtering akin to IGMPv3—ensuring consistent multicast behavior across IP versions without direct protocol-level interaction between IGMP and MLD.[12][13] While IGMP has no direct interaction with unicast protocols such as ICMP, its reliance on the IP layer provides indirect connectivity, as IGMP datagrams traverse the same IP infrastructure used for unicast traffic.[9]Protocol Versions
IGMPv1
IGMPv1, the initial version of the Internet Group Management Protocol, was specified in 1989 to enable hosts to report their multicast group memberships to adjacent routers on IPv4 networks.[14] It operates using IP protocol number 2 and supports any-source multicast (ASM), where traffic from any source address can be received for a group without source-specific filtering.[14] Hosts join a multicast group by invoking a socket option and immediately transmitting a membership report to the group address, ensuring prompt inclusion in the forwarding state.[14] Routers maintain membership information through periodic general queries sent to the all-hosts address (224.0.0.1) with a TTL of 1, typically at intervals not exceeding 60 seconds to minimize overhead while refreshing group states.[14] The protocol defines only two message types in a fixed 8-byte format: Host Membership Query (type 1), which has a group address field set to zero for general queries, and Host Membership Report (type 2), which specifies the group address for which membership is being reported.[14] Each message includes a version field (set to 1), type, unused bits, checksum, and the 32-bit group address.[14] To prevent report implosion on shared networks, hosts delay their responses randomly between 0 and 10 seconds upon receiving a query, and suppress duplicate reports if they overhear another host's report for the same group.[14] Leaving a group occurs silently without an explicit message; hosts simply cease reporting, and routers infer departure from the absence of responses to subsequent queries.[14] A key limitation of IGMPv1 is the lack of group-specific queries, restricting routers to broadcasting general queries that solicit reports for all groups, which increases network traffic and delays detection of membership changes.[3] Without an explicit leave mechanism, leave detection relies on query timeouts, potentially delaying the pruning of forwarding state by up to 3 minutes as routers wait for non-responses over multiple query cycles.[3] This inefficiency, combined with no support for source-specific multicast, makes IGMPv1 unsuitable for modern bandwidth-sensitive applications.[15] For backward compatibility in mixed networks, subsequent versions like IGMPv2 and IGMPv3 default to IGMPv1 behavior when version 1 routers are detected, ensuring interoperability with legacy systems.[3] IGMPv1 is rarely used standalone today, though it is emulated in newer implementations for supporting legacy hosts.[16]IGMPv2
IGMPv2, defined in RFC 2236 in November 1997, builds upon IGMPv1 by introducing mechanisms to optimize multicast group membership reporting and router processing in IPv4 networks. A primary enhancement is the addition of the Leave Group message (type 0x17), which permits hosts to promptly inform adjacent routers of their exit from a multicast group, thereby shortening the leave latency from up to three minutes in IGMPv1 to mere seconds. This immediate notification prevents unnecessary traffic forwarding to vacated hosts. IGMPv2 also supports group-specific queries, enabling routers to target inquiries to individual groups for more precise membership verification.[3] The protocol employs three core message types to manage group dynamics: Membership Query (type 0x11), which incorporates a Maximum Response Time field in hundredths of a second to stagger host responses and mitigate traffic bursts, along with the querier's IP address derived from the packet source; Version 2 Membership Report (type 0x16), used by hosts to affirm ongoing group interest; and Leave Group (type 0x17). Messages follow a variable-length format starting with an 8-octet header, and the protocol includes a configurable robustness variable—defaulting to 2—to retransmit queries in lossy environments, enhancing reliability without excessive overhead.[3] Operational efficiency is further improved through a deterministic querier election process, where the router with the lowest IP address on the subnet assumes the querier role upon detecting competing queries. For backward compatibility, IGMPv2 routers detect IGMPv1 hosts by parsing the distinct report format lacking the Maximum Response Time field and can revert to v1 behavior if needed. RFC 2236 formally obsoletes RFC 1112, the specification for IGMPv1, while preserving interoperability.[3] Despite these advances, IGMPv2 operates exclusively in an any-source multicast model, forwarding all sources to interested groups without provisions for source-specific filtering—a capability deferred to IGMPv3.[3]IGMPv3
IGMPv3 introduces support for source-specific multicast (SSM), enabling hosts to report interest in multicast traffic from specific sources rather than all sources for a group. This is achieved through two filter modes in membership reports: INCLUDE, where hosts specify the desired sources from which they want to receive traffic for a group, and EXCLUDE, where hosts indicate sources to block while receiving from all others. These modes allow for more precise control over multicast reception, facilitating applications that require selective source filtering.[1] The protocol defines two primary message types: the Membership Query (type 0x11), which routers use to poll hosts and can include a source list to query specific source-group combinations, and the Membership Report (type 0x22), sent by hosts to convey their current state with records specifying the filter mode (INCLUDE or EXCLUDE) along with associated source addresses. These reports support multiple group records in a single message, enhancing efficiency in state reporting.[17][1] Key improvements in IGMPv3 include an extended default Query Interval of 125 seconds between general queries, reducing network overhead compared to prior versions. The protocol also incorporates updates from RFC 4604, which refine state diagrams, timers, and behaviors for SSM-aware routers and hosts to ensure consistent handling of source-specific joins and compatibility in mixed environments.[15][6] For backward compatibility, IGMPv3 routers maintain per-interface modes that negotiate down to IGMPv1 or v2 when older reports are detected, ensuring seamless operation in heterogeneous networks. All IGMPv3 membership reports are sent to the all-IGMPv3-routers address 224.0.0.22, which all version-capable devices monitor.[1][1] Adoption of IGMPv3 has been driven by its ability to enable bandwidth savings in multicast applications, such as video-on-demand, by allowing hosts to filter out unwanted sources and receive only relevant streams, thereby optimizing network resource utilization in scenarios with multiple content providers.[6]Message Types and Formats
Common Message Structure
IGMP messages are encapsulated as payloads within IPv4 datagrams, using IP protocol number 2 to indicate the protocol.[18][9][19] The IPv4 header for these datagrams specifies a time-to-live (TTL) value of 1, ensuring the messages are processed only by the local network.[9][19] For query messages, the destination IP address is set to 224.0.0.1 (the all-hosts multicast address), while report messages use the multicast group address as the destination.[9][19] The core IGMP header, applicable to versions 1 and 2, consists of 8 octets with the following fixed fields: a 1-octet Type field indicating the message type; a 1-octet Max Resp Time (or Code in version 3) field specifying the maximum response time for queries; a 2-octet Checksum field for integrity verification; and a 4-octet Group Address field containing the multicast group address (set to 0.0.0.0 for general queries).[18][9]| Field | Size (octets) | Description |
|---|---|---|
| Type | 1 | Identifies the IGMP message type (e.g., query or report). |
| Max Resp Time/Code | 1 | Maximum response time in 1/10-second units for queries; used for version detection. |
| Checksum | 2 | 16-bit one's complement checksum of the IGMP message. |
| Group Address | 4 | IPv4 multicast address of the group; zero for general queries. |
Query Messages
Query messages in the Internet Group Management Protocol (IGMP) are initiated by multicast routers, known as queriers, to poll hosts for their multicast group memberships on a local network. These messages enable routers to maintain accurate records of group subscriptions, ensuring efficient multicast traffic forwarding. In all versions of IGMP, queries are sent with an IP destination address of 224.0.0.1 (the all-systems multicast address) for general queries, and an IP time-to-live (TTL) value of 1 to limit scope to the local subnet.[2][3][1] In IGMPv1, the only query type is the General Query, which solicits reports from all groups on the subnet. Its structure consists of an 8-octet message with Type field set to 1, an Unused field (zeroed on transmission), a 16-bit Checksum, and a Group Address field (zeroed on transmission and ignored on reception). General Queries in IGMPv1 are sent periodically, no more frequently than once per minute, or in rapid succession during router startup to quickly ascertain memberships. Hosts receiving a valid General Query start a random delay timer between 0 and 10 seconds before responding, suppressing responses if another host reports first.[2] IGMPv2 introduces both General and Group-Specific Queries, expanding querier capabilities. The General Query, with Type 0x11 and Group Address 0, discovers all active groups, sent periodically at the Query Interval (default 125 seconds). The Group-Specific Query, with Type 0x11 and the target Group Address set, confirms lingering memberships after a host sends a Leave Group message, transmitted up to the Last Member Query Count (default equal to the Robustness Variable, typically 2) times at 1-second intervals. Both query types include a Max Resp Time field (default 10 seconds for General Queries), specifying the maximum host response delay in tenths of a second. The Querier's Robustness Variable (QRV, default 2) and Querier's Query Interval Code (QQIC, encoding the 125-second default) are conveyed in the unused octet of IGMPv1 queries but repurposed in IGMPv2 for robustness against packet loss and interval tuning. Response suppression occurs if a host hears a report for the queried group within the Max Resp Time, preventing redundant transmissions.[3] IGMPv3 builds on prior versions with three query variants: General, Group-Specific, and Group-and-Source-Specific, all using Type 0x11, as specified in RFC 9776 (2025), which obsoletes RFC 3376. The General Query (Group Address 0, Number of Sources (S) 0) polls for all group memberships, sent periodically at the Query Interval derived from QQIC (default 125 seconds). The Group-Specific Query (Group Address set, S=0) verifies members for a single group, typically after leave detection, with a shorter Max Resp Code (default 1 second). The Group-and-Source-Specific Query (Group Address set, S>0, followed by a Source Address list) checks reception from particular sources in INCLUDE mode filter states, used to confirm source-specific subscriptions. Unique to IGMPv3 queries, the Suppress Router Processing (S) flag, located in the octet following the Group Address, when set to 1 instructs receiving multicast routers to suppress their timer updates in response to the query, aiding compatibility in mixed-version environments. The QRV field (default 2 if zero) and QQIC field (default 125 seconds if zero) are explicitly included, with the Max Resp Code using linear scaling below 128 (in tenths of a second) and exponential above for longer delays up to about 53 minutes. Queries include an S field indicating the number of source addresses (0 for non-source-specific types), followed by the unicast Source Address list when S>0. Timing follows the querier's interval, with elected queriers (lowest IP address) sending queries; lower-IP queriers override others upon detection.[1]Report and Leave Messages
In IGMP versions 1 and 2, hosts send Membership Report messages to inform routers of their interest in receiving traffic for specific multicast groups. The IGMPv1 Membership Report has a message type of 0x12 and consists of the type field, an unused field set to zero, a checksum, and the multicast group address.[2] These reports are sent either unicast to a specific router or multicast to the group address itself, with an IP TTL of 1.[2] Similarly, the IGMPv2 Membership Report uses type 0x16, includes the same fields plus a Max Response Time set to zero, and follows the same transmission rules.[3] Both versions limit the report to a single group address, without source-specific details.[3] IGMPv3 introduces a more flexible Membership Report structure with type 0x22, allowing multiple group records in a single message to support source-specific filtering.[1] Each group record includes a record type—such as MODE_IS_INCLUDE (value 1) for receiving traffic only from specified sources or MODE_IS_EXCLUDE (value 2) for receiving from all sources except those listed—an auxiliary data length (typically zero in standard IGMPv3), the number of sources (N), the multicast group address, and a source list of N unicast IP addresses.[1] These reports are sent multicast to the all-IGMPv3-routers address 224.0.0.22, enabling efficient batch reporting of include or exclude modes for multiple groups and sources.[1] IGMPv3 group records use the following record types:- MODE_IS_INCLUDE (1): Current state is INCLUDE mode; the interface receives traffic only from the listed sources.
- MODE_IS_EXCLUDE (2): Current state is EXCLUDE mode; the interface receives traffic from all sources except those listed.
- CHANGE_TO_INCLUDE_MODE (3, TO_IN): The filter mode has changed to INCLUDE; the source list specifies the new desired sources. Commonly used when switching to source-specific multicast (SSM) or signaling a leave by using an empty list (TO_IN {}).
- CHANGE_TO_EXCLUDE_MODE (4, TO_EX): The filter mode has changed to EXCLUDE; the source list specifies sources to exclude. Often used for standard group joins in any-source multicast (ASM) with an empty source list (TO_EX {}), equivalent to a general join.
- ALLOW_NEW_SOURCES (5): Adds new sources to the existing include list (sent in state-change reports).
- BLOCK_OLD_SOURCES (6): Removes sources from the include list or adds to exclude (sent in state-change reports).