Recent from talks
Nothing was collected or created yet.
Advanced Encryption Standard
View on Wikipedia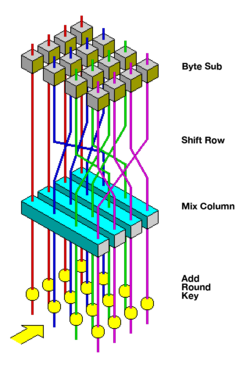 Visualization of the AES round function | |
| General | |
|---|---|
| Designers | Joan Daemen, Vincent Rijmen |
| First published | 1998 |
| Derived from | Square |
| Successors | Anubis, Grand Cru, Kalyna |
| Certification | AES winner, CRYPTREC, NESSIE, NSA |
| Cipher detail | |
| Key sizes | 128, 192 or 256 bits[note 1] |
| Block sizes | 128 bits[note 2] |
| Structure | Substitution–permutation network |
| Rounds | 10, 12 or 14 (depending on key size) |
| Best public cryptanalysis | |
| Attacks have been published that are computationally faster than a full brute-force attack, though none as of 2023 are computationally feasible.[1]
For AES-128, the key can be recovered with a computational complexity of 2126.1 using the biclique attack. For biclique attacks on AES-192 and AES-256, the computational complexities of 2189.7 and 2254.4 respectively apply. Related-key attacks can break AES-192 and AES-256 with complexities 299.5 and 2176 in both time and data, respectively.[2] Another attack was blogged[3] and released as a preprint[4] in 2009. This attack is against AES-256 that uses only two related keys and 239 time to recover the complete 256-bit key of a 9-round version, or 245 time for a 10-round version with a stronger type of related subkey attack, or 270 time for an 11-round version. | |
The Advanced Encryption Standard (AES), also known by its original name Rijndael (Dutch pronunciation: [ˈrɛindaːl]),[5] is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001.[6]
AES is a variant of the Rijndael block cipher[5] developed by two Belgian cryptographers, Joan Daemen and Vincent Rijmen, who submitted a proposal[7] to NIST during the AES selection process.[8] Rijndael is a family of ciphers with different key and block sizes. For AES, NIST selected three members of the Rijndael family, each with a block size of 128 bits, but three different key lengths: 128, 192 and 256 bits.
AES has been adopted by the U.S. government. It supersedes the Data Encryption Standard (DES),[9] which was published in 1977. The algorithm described by AES is a symmetric-key algorithm, meaning the same key is used for both encrypting and decrypting the data.
In the United States, AES was announced by the NIST as U.S. FIPS PUB 197 (FIPS 197) on November 26, 2001.[6] This announcement followed a five-year standardization process in which fifteen competing designs were presented and evaluated, before the Rijndael cipher was selected as the most suitable.
AES is included in the ISO/IEC 18033-3 standard. AES became effective as a U.S. federal government standard on May 26, 2002, after approval by U.S. Secretary of Commerce Donald Evans. AES is available in many different encryption packages, and is the first (and only) publicly accessible cipher approved by the U.S. National Security Agency (NSA) for top secret information when used in an NSA approved cryptographic module.[note 3]
Definitive standards
[edit]The Advanced Encryption Standard (AES) is defined in each of:
Description of the ciphers
[edit]AES is based on a design principle known as a substitution–permutation network, and is efficient in both software and hardware.[11] Unlike its predecessor DES, AES does not use a Feistel network. AES is a variant of Rijndael, with a fixed block size of 128 bits, and a key size of 128, 192, or 256 bits. By contrast, Rijndael per se is specified with block and key sizes that may be any multiple of 32 bits, with a minimum of 128 and a maximum of 256 bits. Most AES calculations are done in a particular finite field.
AES operates on a 4 × 4 column-major order array of 16 bytes b0, b1, ..., b15 termed the state:[note 4]
The key size used for an AES cipher specifies the number of transformation rounds that convert the input, called the plaintext, into the final output, called the ciphertext. The number of rounds are as follows:
- 10 rounds for 128-bit keys.
- 12 rounds for 192-bit keys.
- 14 rounds for 256-bit keys.
Each round consists of several processing steps, including one that depends on the encryption key itself. A set of reverse rounds are applied to transform ciphertext back into the original plaintext using the same encryption key.
High-level description of the algorithm
[edit]- KeyExpansion – round keys are derived from the cipher key using the AES key schedule. AES requires a separate 128-bit round key block for each round plus one more.
- Initial round key addition:
- AddRoundKey – each byte of the state is combined with a byte of the round key using bitwise xor.
- 9, 11 or 13 rounds:
- SubBytes – a non-linear substitution step where each byte is replaced with another according to a lookup table.
- ShiftRows – a transposition step where the last three rows of the state are shifted cyclically a certain number of steps.
- MixColumns – a linear mixing operation which operates on the columns of the state, combining the four bytes in each column.
- AddRoundKey
- Final round (making 10, 12 or 14 rounds in total):
- SubBytes
- ShiftRows
- AddRoundKey
The SubBytes step
[edit]
In the SubBytes step, each byte in the state array is replaced with a SubByte using an 8-bit substitution box. Before round 0, the state array is simply the plaintext/input. This operation provides the non-linearity in the cipher. The S-box used is derived from the multiplicative inverse over GF(28), known to have good non-linearity properties. To avoid attacks based on simple algebraic properties, the S-box is constructed by combining the inverse function with an invertible affine transformation. The S-box is also chosen to avoid any fixed points (and so is a derangement), i.e., , and also any opposite fixed points, i.e., . While performing the decryption, the InvSubBytes step (the inverse of SubBytes) is used, which requires first taking the inverse of the affine transformation and then finding the multiplicative inverse.
The ShiftRows step
[edit]
The ShiftRows step operates on the rows of the state; it cyclically shifts the bytes in each row by a certain offset. For AES, the first row is left unchanged. Each byte of the second row is shifted one to the left. Similarly, the third and fourth rows are shifted by offsets of two and three respectively.[note 5] In this way, each column of the output state of the ShiftRows step is composed of bytes from each column of the input state. The importance of this step is to avoid the columns being encrypted independently, in which case AES would degenerate into four independent block ciphers.
The MixColumns step
[edit]
In the MixColumns step, the four bytes of each column of the state are combined using an invertible linear transformation. The MixColumns function takes four bytes as input and outputs four bytes, where each input byte affects all four output bytes. Together with ShiftRows, MixColumns provides diffusion in the cipher.
During this operation, each column is transformed using a fixed matrix (matrix left-multiplied by column gives new value of column in the state):
Matrix multiplication is composed of multiplication and addition of the entries. Entries are bytes treated as coefficients of polynomial of order . Addition is simply XOR. Multiplication is modulo irreducible polynomial . If processed bit by bit, then, after shifting, a conditional XOR with 1B16 should be performed if the shifted value is larger than FF16 (overflow must be corrected by subtraction of generating polynomial). These are special cases of the usual multiplication in .
In more general sense, each column is treated as a polynomial over and is then multiplied modulo with a fixed polynomial . The coefficients are displayed in their hexadecimal equivalent of the binary representation of bit polynomials from . The MixColumns step can also be viewed as a multiplication by the shown particular MDS matrix in the finite field . This process is described further in the article Rijndael MixColumns.
The AddRoundKey
[edit]
In the AddRoundKey step, the subkey is combined with the state. For each round, a subkey is derived from the main key using Rijndael's key schedule; each subkey is the same size as the state. The subkey is added by combining of the state with the corresponding byte of the subkey using bitwise XOR.
Optimization of the cipher
[edit]On systems with 32-bit or larger words, it is possible to speed up execution of this cipher by combining the SubBytes and ShiftRows steps with the MixColumns step by transforming them into a sequence of table lookups. This requires four 256-entry 32-bit tables (together occupying 4096 bytes). A round can then be performed with 16 table lookup operations and 12 32-bit exclusive-or operations, followed by four 32-bit exclusive-or operations in the AddRoundKey step.[12] Alternatively, the table lookup operation can be performed with a single 256-entry 32-bit table (occupying 1024 bytes) followed by circular rotation operations.
Using a byte-oriented approach, it is possible to combine the SubBytes, ShiftRows, and MixColumns steps into a single round operation.[13]
Security
[edit]The National Security Agency (NSA) reviewed all the AES finalists, including Rijndael, and stated that all of them were secure enough for U.S. Government non-classified data. In June 2003, the U.S. Government announced that AES could be used to protect classified information:
The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require use of either the 192 or 256 key lengths. The implementation of AES in products intended to protect national security systems and/or information must be reviewed and certified by NSA prior to their acquisition and use.[14]
AES has 10 rounds for 128-bit keys, 12 rounds for 192-bit keys, and 14 rounds for 256-bit keys.
Known attacks
[edit]For cryptographers, a cryptographic "break" is anything faster than a brute-force attack— i.e., performing one trial decryption for each possible key in sequence . A break can thus include results that are infeasible with current technology. Despite being impractical, theoretical breaks can sometimes provide insight into vulnerability patterns. The largest successful publicly known brute-force attack against a widely implemented block-cipher encryption algorithm was against a 64-bit RC5 key by distributed.net in 2006.[15]
The key space increases by a factor of 2 for each additional bit of key length, and if every possible value of the key is equiprobable; this translates into a doubling of the average brute-force key search time with every additional bit of key length. This implies that the effort of a brute-force search increases exponentially with key length. Key length in itself does not imply security against attacks, since there are ciphers with very long keys that have been found to be vulnerable.
AES has a fairly simple algebraic framework.[16] In 2002, a theoretical attack, named the "XSL attack", was announced by Nicolas Courtois and Josef Pieprzyk, purporting to show a weakness in the AES algorithm, partially due to the low complexity of its nonlinear components.[17] Since then, other papers have shown that the attack, as originally presented, is unworkable; see XSL attack on block ciphers.
During the AES selection process, developers of competing algorithms wrote of Rijndael's algorithm "we are concerned about [its] use ... in security-critical applications."[18] In October 2000, however, at the end of the AES selection process, Bruce Schneier, a developer of the competing algorithm Twofish, wrote that while he thought successful academic attacks on Rijndael would be developed someday, he "did not believe that anyone will ever discover an attack that will allow someone to read Rijndael traffic."[19]
By 2006, the best known attacks were on 7 rounds for 128-bit keys, 8 rounds for 192-bit keys, and 9 rounds for 256-bit keys.[20]
Until May 2009, the only successful published attacks against the full AES were side-channel attacks on some specific implementations. In 2009, a new related-key attack was discovered that exploits the simplicity of AES's key schedule and has a complexity of 2119. In December 2009 it was improved to 299.5.[2] This is a follow-up to an attack discovered earlier in 2009 by Alex Biryukov, Dmitry Khovratovich, and Ivica Nikolić, with a complexity of 296 for one out of every 235 keys.[21] However, related-key attacks are not of concern in any properly designed cryptographic protocol, as a properly designed protocol (i.e., implementational software) will take care not to allow related keys, essentially by constraining an attacker's means of selecting keys for relatedness.
Another attack was blogged by Bruce Schneier[3] on July 30, 2009, and released as a preprint[22] on August 3, 2009. This new attack, by Alex Biryukov, Orr Dunkelman, Nathan Keller, Dmitry Khovratovich, and Adi Shamir, is against AES-256 that uses only two related keys and 239 time to recover the complete 256-bit key of a 9-round version, or 245 time for a 10-round version with a stronger type of related subkey attack, or 270 time for an 11-round version. 256-bit AES uses 14 rounds, so these attacks are not effective against full AES.
The practicality of these attacks with stronger related keys has been criticized,[23] for instance, by the paper on chosen-key-relations-in-the-middle attacks on AES-128 authored by Vincent Rijmen in 2010.[24]
In November 2009, the first known-key distinguishing attack against a reduced 8-round version of AES-128 was released as a preprint.[25] This known-key distinguishing attack is an improvement of the rebound, or the start-from-the-middle attack, against AES-like permutations, which view two consecutive rounds of permutation as the application of a so-called Super-S-box. It works on the 8-round version of AES-128, with a time complexity of 248, and a memory complexity of 232. 128-bit AES uses 10 rounds, so this attack is not effective against full AES-128.
The first key-recovery attacks on full AES were by Andrey Bogdanov, Dmitry Khovratovich, and Christian Rechberger, and were published in 2011.[26] The attack is a biclique attack and is faster than brute force by a factor of about four. It requires 2126.2 operations to recover an AES-128 key. For AES-192 and AES-256, 2190.2 and 2254.6 operations are needed, respectively. This result has been further improved to 2126.0 for AES-128, 2189.9 for AES-192, and 2254.3 for AES-256 by Biaoshuai Tao and Hongjun Wu in a 2015 paper,[27] which are the current best results in key recovery attack against AES.
This is a very small gain, as a 126-bit key (instead of 128 bits) would still take billions of years to brute force on current and foreseeable hardware. Also, the authors calculate the best attack using their technique on AES with a 128-bit key requires storing 288 bits of data. That works out to about 38 trillion terabytes of data, which was more than all the data stored on all the computers on the planet in 2016.[28] A paper in 2015 later improved the space complexity to 256 bits,[27] which is 9007 terabytes (while still keeping a time complexity of approximately 2126).
According to the Snowden documents, the NSA is doing research on whether a cryptographic attack based on tau statistic may help to break AES.[29]
At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented.[citation needed]
Side-channel attacks
[edit]Side-channel attacks do not attack the cipher as a black box, and thus are not related to cipher security as defined in the classical context, but are important in practice. They attack implementations of the cipher on hardware or software systems that inadvertently leak data. There are several such known attacks on various implementations of AES.
In April 2005, D. J. Bernstein announced a cache-timing attack that he used to break a custom server that used OpenSSL's AES encryption.[30] The attack required over 200 million chosen plaintexts.[31] The custom server was designed to give out as much timing information as possible (the server reports back the number of machine cycles taken by the encryption operation). However, as Bernstein pointed out, "reducing the precision of the server's timestamps, or eliminating them from the server's responses, does not stop the attack: the client simply uses round-trip timings based on its local clock, and compensates for the increased noise by averaging over a larger number of samples."[30]
In October 2005, Dag Arne Osvik, Adi Shamir and Eran Tromer presented a paper demonstrating several cache-timing attacks against the implementations in AES found in OpenSSL and Linux's dm-crypt partition encryption function.[32] One attack was able to obtain an entire AES key after only 800 operations triggering encryptions, in a total of 65 milliseconds. This attack requires the attacker to be able to run programs on the same system or platform that is performing AES.
In December 2009 an attack on some hardware implementations was published that used differential fault analysis and allows recovery of a key with a complexity of 232.[33]
In November 2010 Endre Bangerter, David Gullasch and Stephan Krenn published a paper which described a practical approach to a "near real time" recovery of secret keys from AES-128 without the need for either cipher text or plaintext. The approach also works on AES-128 implementations that use compression tables, such as OpenSSL.[34] Like some earlier attacks, this one requires the ability to run unprivileged code on the system performing the AES encryption, which may be achieved by malware infection far more easily than commandeering the root account.[35]
In March 2016, C. Ashokkumar, Ravi Prakash Giri and Bernard Menezes presented a side-channel attack on AES implementations that can recover the complete 128-bit AES key in just 6–7 blocks of plaintext/ciphertext, which is a substantial improvement over previous works that require between 100 and a million encryptions.[36] The proposed attack requires standard user privilege and key-retrieval algorithms run under a minute.
Many modern CPUs have built-in hardware instructions for AES, which protect against timing-related side-channel attacks.[37][38]
Quantum attacks
[edit]AES-256 is considered to be quantum resistant, as it has similar quantum resistance to AES-128's resistance against traditional, non-quantum, attacks at 128 bits of security. AES-192 and AES-128 are not considered quantum resistant due to their smaller key sizes. AES-192 has a strength of 96 bits against quantum attacks and AES-128 has 64 bits of strength against quantum attacks, making them both insecure.[39][40]
NIST/CSEC validation
[edit]The Cryptographic Module Validation Program (CMVP) is operated jointly by the United States Government's National Institute of Standards and Technology (NIST) Computer Security Division and the Communications Security Establishment (CSE) of the Government of Canada. The use of cryptographic modules validated to NIST FIPS 140-2 is required by the United States Government for encryption of all data that has a classification of Sensitive but Unclassified (SBU) or above. From NSTISSP #11, National Policy Governing the Acquisition of Information Assurance: "Encryption products for protecting classified information will be certified by NSA, and encryption products intended for protecting sensitive information will be certified in accordance with NIST FIPS 140-2."[41]
The Government of Canada also recommends the use of FIPS 140 validated cryptographic modules in unclassified applications of its departments.
Although NIST publication 197 ("FIPS 197") is the unique document that covers the AES algorithm, vendors typically approach the CMVP under FIPS 140 and ask to have several algorithms (such as Triple DES or SHA1) validated at the same time. Therefore, it is rare to find cryptographic modules that are uniquely FIPS 197 validated and NIST itself does not generally take the time to list FIPS 197 validated modules separately on its public web site. Instead, FIPS 197 validation is typically just listed as an "FIPS approved: AES" notation (with a specific FIPS 197 certificate number) in the current list of FIPS 140 validated cryptographic modules.
The Cryptographic Algorithm Validation Program (CAVP)[42] allows for independent validation of the correct implementation of the AES algorithm. Successful validation results in being listed on the NIST validations page.[43] This testing is a pre-requisite for the FIPS 140-2 module validation. However, successful CAVP validation in no way implies that the cryptographic module implementing the algorithm is secure. A cryptographic module lacking FIPS 140-2 validation or specific approval by the NSA is not deemed secure by the US Government and cannot be used to protect government data.[41]
FIPS 140-2 validation is challenging to achieve both technically and fiscally.[44] There is a standardized battery of tests as well as an element of source code review that must be passed over a period of a few weeks. The cost to perform these tests through an approved laboratory can be significant (e.g., well over US$30,000)[44] and does not include the time it takes to write, test, document and prepare a module for validation. After validation, modules must be re-submitted and re-evaluated if they are changed in any way. This can vary from simple paperwork updates if the security functionality did not change to a more substantial set of re-testing if the security functionality was impacted by the change.
Test vectors
[edit]Test vectors are a set of known ciphers for a given input and key. NIST distributes the reference of AES test vectors as AES Known Answer Test (KAT) Vectors.[note 6]
Performance
[edit]High speed and low RAM requirements were some of the criteria of the AES selection process. As the chosen algorithm, AES performed well on a wide variety of hardware, from 8-bit smart cards to high-performance computers.
On a Pentium Pro, AES encryption requires 18 clock cycles per byte (cpb),[45] equivalent to a throughput of about 11 MiB/s for a 200 MHz processor.
On Intel Core and AMD Ryzen CPUs supporting AES-NI instruction set extensions, throughput can be multiple GiB/s.[46] On an Intel Westmere CPU, AES encryption using AES-NI takes about 1.3 cpb for AES-128 and 1.8 cpb for AES-256.[47]
Implementations
[edit]See also
[edit]- AES modes of operation
- Disk encryption
- Whirlpool – hash function created by Vincent Rijmen and Paulo S. L. M. Barreto
- List of free and open-source software packages
Notes
[edit]- ^ Key sizes of 128, 160, 192, 224, and 256 bits are supported by the Rijndael algorithm, but only the 128, 192, and 256-bit key sizes are specified in the AES standard.
- ^ Block sizes of 128, 160, 192, 224, and 256 bits are supported by the Rijndael algorithm for each key size, but only the 128-bit block size is specified in the AES standard.
- ^ See Security of AES below.
- ^ Large-block variants of Rijndael use an array with additional columns, but always four rows.
- ^ Rijndael variants with a larger block size have slightly different offsets. For blocks of sizes 128 bits and 192 bits, the shifting pattern is the same. Row is shifted left circular by bytes. For a 256-bit block, the first row is unchanged and the shifting for the second, third and fourth row is 1 byte, 3 bytes and 4 bytes respectively—this change only applies for the Rijndael cipher when used with a 256-bit block, as AES does not use 256-bit blocks.
- ^ The AES Known Answer Test (KAT) Vectors are available in Zip format within the NIST site here Archived 2009-10-23 at the Wayback Machine
References
[edit]- ^ "Biclique Cryptanalysis of the Full AES" (PDF). Archived from the original (PDF) on March 6, 2016. Retrieved May 1, 2019.
- ^ a b Alex Biryukov and Dmitry Khovratovich, Related-key Cryptanalysis of the Full AES-192 and AES-256, "Related-key Cryptanalysis of the Full AES-192 and AES-256". Table 1. Archived from the original on 2009-09-28. Retrieved 2010-02-16.
- ^ a b Bruce Schneier (2009-07-30). "Another New AES Attack". Schneier on Security, A blog covering security and security technology. Archived from the original on 2009-10-05. Retrieved 2010-03-11.
- ^ Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19). "Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds". Archived from the original on 28 January 2010. Retrieved 2010-03-11.
- ^ a b Daemen, Joan; Rijmen, Vincent (March 9, 2003). "AES Proposal: Rijndael" (PDF). National Institute of Standards and Technology. p. 1. Archived (PDF) from the original on 5 March 2013. Retrieved 21 February 2013.
- ^ a b c "Announcing the ADVANCED ENCRYPTION STANDARD (AES)" (PDF). Federal Information Processing Standards Publication 197. United States National Institute of Standards and Technology (NIST). November 26, 2001. Archived (PDF) from the original on August 23, 2024. Retrieved August 26, 2024.
- ^ Joan Daemen and Vincent Rijmen (September 3, 1999). "AES Proposal: Rijndael" (PDF). Archived from the original (PDF) on February 3, 2007.
- ^ Schwartz, John (October 3, 2000). "U.S. Selects a New Encryption Technique". The New York Times. Archived from the original on March 28, 2017.
- ^ Westlund, Harold B. (2002). "NIST reports measurable success of Advanced Encryption Standard". Journal of Research of the National Institute of Standards and Technology. Archived from the original on 2007-11-03.
- ^ "ISO/IEC 18033-3: Information technology – Security techniques – Encryption algorithms – Part 3: Block ciphers". Archived from the original on 2013-12-03.
- ^ Bruce Schneier; John Kelsey; Doug Whiting; David Wagner; Chris Hall; Niels Ferguson; Tadayoshi Kohno; et al. (May 2000). "The Twofish Team's Final Comments on AES Selection" (PDF). Archived (PDF) from the original on 2010-01-02.
- ^ Bertoni, Guido; Breveglieri, Luca; Fragneto, Pasqualina; MacChetti, Marco; Marchesin, Stefano (2003). "Efficient Software Implementation of AES on 32-Bit Platforms". Cryptographic Hardware and Embedded Systems - CHES 2002. Lecture Notes in Computer Science. Vol. 2523. pp. 159–171. doi:10.1007/3-540-36400-5_13. ISBN 978-3-540-00409-7.
- ^ "byte-oriented-aes – A public domain byte-oriented implementation of AES in C – Google Project Hosting". Archived from the original on 2013-07-20. Retrieved 2012-12-23.
- ^ Lynn Hathaway (June 2003). "National Policy on the Use of the Advanced Encryption Standard (AES) to Protect National Security Systems and National Security Information" (PDF). Archived (PDF) from the original on 2010-11-06. Retrieved 2011-02-15.
- ^ Ou, George (April 30, 2006). "Is encryption really crackable?". Ziff-Davis. Archived from the original on August 8, 2010. Retrieved August 7, 2010.
- ^ "Sean Murphy". University of London. Archived from the original on 2009-01-31. Retrieved 2008-11-02.
- ^ Bruce Schneier. "AES News, Crypto-Gram Newsletter, September 15, 2002". Archived from the original on 7 July 2007. Retrieved 2007-07-27.
- ^ Niels Ferguson; Richard Schroeppel; Doug Whiting (2001). "A simple algebraic representation of Rijndael". Proceedings of Selected Areas in Cryptography, 2001, Lecture Notes in Computer Science. Springer-Verlag. pp. 103–111. CiteSeerX 10.1.1.28.4921. Archived from the original (PDF/PostScript) on 4 November 2006. Retrieved 2006-10-06.
- ^ Bruce Schneier, AES Announced Archived 2009-02-01 at the Wayback Machine, October 15, 2000
- ^ John Kelsey, Stefan Lucks, Bruce Schneier, Mike Stay, David Wagner, and Doug Whiting, Improved Cryptanalysis of Rijndael, Fast Software Encryption, 2000 pp213–230 "Academic: Improved Cryptanalysis of Rijndael - Schneier on Security". Archived from the original on 2007-02-23. Retrieved 2007-03-06.
- ^ Nikolić, Ivica (2009). "Distinguisher and Related-Key Attack on the Full AES-256". Advances in Cryptology - CRYPTO 2009. Lecture Notes in Computer Science. Vol. 5677. Springer Berlin / Heidelberg. pp. 231–249. doi:10.1007/978-3-642-03356-8_14. ISBN 978-3-642-03355-1.
- ^ Alex Biryukov; Orr Dunkelman; Nathan Keller; Dmitry Khovratovich; Adi Shamir (2009-08-19). "Key Recovery Attacks of Practical Complexity on AES Variants With Up To 10 Rounds". Archived from the original on 28 January 2010. Retrieved 2010-03-11.
- ^ Agren, Martin (2012). On Some Symmetric Lightweight Cryptographic Designs. Dissertation, Lund University. pp. 38–39.
- ^ Vincent Rijmen (2010). "Practical-Titled Attack on AES-128 Using Chosen-Text Relations" (PDF). IACR Cryptology ePrint Archive. Archived (PDF) from the original on 2010-07-02.
- ^ Henri Gilbert; Thomas Peyrin (2009-11-09). "Super-Sbox Cryptanalysis: Improved Attacks for AES-like permutations". IACR Cryptology ePrint Archive. Archived from the original on 2010-06-04. Retrieved 2010-03-11.
- ^ Bogdanov, Andrey; Khovratovich, Dmitry; Rechberger, Christian (2011). "Biclique Cryptanalysis of the Full AES". In Lee, Dong Hoon; Wang, Xiaoyun (eds.). Advances in Cryptology – ASIACRYPT 2011. Lecture Notes in Computer Science. Vol. 7073. pp. 344–371. doi:10.1007/978-3-642-25385-0_19. ISBN 978-3-642-25385-0.
- ^ a b Tao, Biaoshuai; Wu, Hongjun (2015). "Improving the Biclique Cryptanalysis of AES". In Foo, Ernest; Stebila, Douglas (eds.). Information Security and Privacy. Lecture Notes in Computer Science. Vol. 9144. pp. 39–56. doi:10.1007/978-3-319-19962-7_3. ISBN 978-3-319-19962-7.
- ^ Jeffrey Goldberg (2011-08-18). "AES Encryption isn't Cracked". Archived from the original on 8 January 2015. Retrieved 30 December 2014.
- ^ "Prying Eyes: Inside the NSA's War on Internet Security". Spiegel Online. Hamburg, Germany. 28 December 2014. Archived from the original on 24 January 2015. Retrieved 4 September 2015.
- ^ a b "Index of formal scientific papers". Cr.yp.to. Archived from the original on 2008-09-17. Retrieved 2008-11-02.
- ^ Bruce Schneier (17 May 2005). "AES Timing Attack". Archived from the original on 12 February 2007. Retrieved 2007-03-17.
- ^ Dag Arne Osvik; Adi Shamir; Eran Tromer (2005-11-20). "Cache Attacks and Countermeasures: the Case of AES" (PDF). The Cryptographer's Track at RSA Conference 2006. Lecture Notes in Computer Science. Vol. 3860. pp. 1–20. doi:10.1007/11605805_1. ISBN 978-3-540-31033-4. Archived (PDF) from the original on 2006-06-19. Retrieved 2008-11-02.
- ^ Dhiman Saha; Debdeep Mukhopadhyay; Dipanwita RoyChowdhury. "A Diagonal Fault Attack on the Advanced Encryption Standard" (PDF). IACR Cryptology ePrint Archive. Archived (PDF) from the original on 22 December 2009. Retrieved 2009-12-08.
- ^ Endre Bangerter; David Gullasch & Stephan Krenn (2010). "Cache Games – Bringing Access-Based Cache Attacks on AES to Practice" (PDF). IACR Cryptology ePrint Archive. Archived (PDF) from the original on 2010-12-14.
- ^ "Breaking AES-128 in realtime, no ciphertext required". Hacker News. Archived from the original on 2011-10-03. Retrieved 2012-12-23.
- ^ Ashokkumar, C.; Giri, Ravi Prakash; Menezes, Bernard (12 May 2016). Highly Efficient Algorithms for AES Key Retrieval in Cache Access Attacks. 2016 IEEE European Symposium on Security and Privacy (EuroS&P). Saarbruecken, Germany. pp. 261–275. doi:10.1109/EuroSP.2016.29.
- ^ Mowery, Keaton; Keelveedhi, Sriram; Shacham, Hovav (19 October 2012). Are AES x86 cache timing attacks still feasible? (PDF). CCS'12: the ACM Conference on Computer and Communications Security. Raleigh, North Carolina, USA. pp. 19–24. doi:10.1145/2381913.2381917. Archived from the original (PDF) on 2017-08-09.
- ^ "Securing the Enterprise with Intel AES-NI" (PDF). Intel Corporation. Archived (PDF) from the original on 2013-03-31. Retrieved 2017-07-26.
- ^ Bonnetain, Xavier; Naya-Plasencia, María; Schrottenloher, André (11 June 2019). "Quantum Security Analysis of AES". IACR Transactions on Symmetric Cryptology. 2019 (2): 55–93. doi:10.13154/tosc.v2019.i2.55-93.
- ^ O'Shea, Dan (April 26, 2022). "AES-256 joins the quantum resistance". Fierce Electronics. Retrieved September 26, 2023.
- ^ a b "NSTISSP No. 11, Revised Fact Sheet, National Information Assurance Acquisition Policy" (PDF). Archived from the original (PDF) on 2012-04-21. Retrieved 2012-05-29.
- ^ "NIST.gov – Computer Security Division – Computer Security Resource Center". Csrc.nist.gov. Archived from the original on 2013-01-02. Retrieved 2012-12-23.
- ^ "Validated FIPS 140-1 and FIPS 140-2 Cryptographic Modules". Archived from the original on 2014-12-26. Retrieved 2014-06-26.
- ^ a b OpenSSL, openssl@openssl.org. "OpenSSL's Notes about FIPS certification". Openssl.org. Archived from the original on 2013-01-02. Retrieved 2012-12-23.
- ^ Schneier, Bruce; Kelsey, John; Whiting, Doug; Wagner, David; Hall, Chris; Ferguson, Niels (1999-02-01). "Performance Comparisons of the AES submissions" (PDF). Archived (PDF) from the original on 2011-06-22. Retrieved 2010-12-28.
- ^ "AMD Ryzen 7 1700X Review".
- ^ "Intel ® Advanced Encryption Standard (AES) New Instructions Set" (PDF). May 2010.
- Courtois, Nicolas; Pieprzyk, Josef (2003). "Cryptanalysis of Block Ciphers with Overdefined Systems of Equations". In Zheng, Yuliang (ed.). Advances in Cryptology – ASIACRYPT 2002: 8th International Conference on the Theory and Application of Cryptology and Information Security, Queenstown, New Zealand, December 1–5, 2002, Proceedings. Springer. pp. 268–287. ISBN 978-3-540-36178-7.
- Daemen, Joan; Rijmen, Vincent (2002). The Design of Rijndael: AES – The Advanced Encryption Standard. Springer. ISBN 978-3-540-42580-9.
- Paar, Christof; Pelzl, Jan (2009). Understanding Cryptography: A Textbook for Students and Practitioners. Springer. pp. 87–122. ISBN 978-3-642-04101-3. alternate link (companion web site contains online lectures on AES)
External links
[edit]- "256bit key – 128bit block – AES". Cryptography – 256 bit Ciphers: Reference source code and submissions to international cryptographic designs contests. EmbeddedSW.
- "Advanced Encryption Standard (AES)" (PDF). Federal Information Processing Standards. 26 November 2001. doi:10.6028/NIST.FIPS.197. 197.
- AES algorithm archive information – (old, unmaintained)
- "Part 3: Block ciphers" (PDF). Information technology – Security techniques – Encryption algorithms (2nd ed.). ISO. 2010-12-15. ISO/IEC 18033-3:2010(E). Archived (PDF) from the original on 2022-10-09.
- Animation of Rijndael – AES deeply explained and animated using Flash (by Enrique Zabala / University ORT / Montevideo / Uruguay). This animation (in English, Spanish, and German) is also part of CrypTool 1 (menu Indiv. Procedures → Visualization of Algorithms → AES).
- HTML5 Animation of Rijndael – Same Animation as above made in HTML5.
- AES Demo in Excel - Example implementation and demonstration in Excel (without macros) by Tim Wambach.
Advanced Encryption Standard
View on GrokipediaHistory and Standardization
Development and Selection Process
By the mid-1990s, the Data Encryption Standard (DES), adopted in 1977 with its 56-bit key length, had become obsolete due to rapid advances in computational power that enabled brute-force attacks to feasibly compromise it, prompting the need for a stronger federal encryption standard.[6] In January 1997, the National Institute of Standards and Technology (NIST) announced its intention to develop a successor, the Advanced Encryption Standard (AES), to protect sensitive but unclassified U.S. government information.[7] On September 12, 1997, NIST issued a formal call for candidate algorithms, specifying requirements for a symmetric block cipher with a 128-bit block size and support for key lengths of 128, 192, and 256 bits, to be royalty-free and publicly reviewed.[6] NIST received 21 submissions by the June 15, 1998 deadline, accepting 15 eligible candidates from submitters in 12 countries, including Rijndael proposed by Belgian cryptographers Joan Daemen and Vincent Rijmen.[6][4] Following an initial screening in 1998 at the First AES Candidate Conference, where the 15 algorithms underwent preliminary cryptanalysis and performance assessments, the evaluation proceeded through two public rounds: a first-round analysis in 1999, narrowing the field to five finalists—MARS, RC6, Rijndael, Serpent, and Twofish—announced on August 9, 1999; and a second-round in-depth review in 2000, leading to the selection of Rijndael.[7] Public comments and expert analyses informed each stage, with conferences in August 1998, March 1999, and April 2000 facilitating global cryptographic community input.[6] In October 2000, after extensive evaluation of the finalists' security margins, software and hardware performance, and ease of implementation across diverse platforms, NIST selected Rijndael for its optimal balance of these attributes, offering strong resistance to known attacks while maintaining high efficiency and flexibility.[6] On October 2, 2000, the U.S. Department of Commerce announced Rijndael as the AES winner, specifying its variants with 128-, 192-, and 256-bit keys to meet varying security needs.[8] This selection marked the culmination of a transparent, international competition that engaged hundreds of cryptographers worldwide.[7] Following its selection and standardization as the Advanced Encryption Standard (AES), Rijndael became the de facto global standard for symmetric block encryption. It is widely adopted in numerous applications, including TLS/HTTPS for secure web communications, disk encryption tools such as BitLocker and FileVault, and VPN protocols, owing to its efficient implementations, broad hardware support, and extensive cryptanalytic auditing by the global community.[9] In contrast, the finalist Serpent, while offering a high security margin, has seen more limited adoption, primarily in niche scenarios such as multi-cipher cascades in VeraCrypt for users seeking additional layers of protection.[10]Definitive Standards and Validation
The Federal Information Processing Standards Publication (FIPS) 197, titled Advanced Encryption Standard (AES), was published by the National Institute of Standards and Technology (NIST) on November 26, 2001.[1] It formally specifies AES as a symmetric block cipher that processes data in fixed 128-bit blocks and supports variable key lengths of 128, 192, or 256 bits, corresponding to AES-128, AES-192, and AES-256 variants, respectively.[1] This standard replaced the older Data Encryption Standard (DES) and established AES as the approved method for protecting sensitive electronic data in federal systems.[1] Internationally, AES was standardized in ISO/IEC 18033-3:2005 as a block cipher for encryption algorithms.[11] On May 9, 2023, NIST issued an updated edition of FIPS 197 (designated FIPS 197-upd1), which incorporated editorial enhancements for clarity, such as improved formatting, reorganized sections, and updated references to current regulations and validation programs, without altering the technical specifications of the AES algorithm.[4] As of November 2025, NIST continues to maintain FIPS 197 through periodic reviews, with no substantive modifications to the core algorithm, reflecting its enduring suitability based on ongoing security assessments like those in NIST IR 8319.[4][2] AES is integral to several other NIST standards that extend its application in secure systems. For message authentication, it integrates with the Keyed-Hash Message Authentication Code (HMAC) mechanism defined in FIPS 198-1, where AES can generate or protect keys for HMAC computations using approved hash functions.[12] More directly, the SP 800-38 series of special publications outlines approved modes of operation for block ciphers like AES, including confidentiality modes (e.g., ECB, CBC, CTR in SP 800-38A) and authenticated encryption modes (e.g., GCM in SP 800-38D, CCM in SP 800-38C).[13] These modes ensure AES's versatility in protocols requiring both encryption and integrity protection.[13] The Canadian Centre for Cyber Security (CCCS), successor to the Communications Security Establishment (CSEC), aligns its cryptographic guidelines with NIST standards and recommends AES for confidentiality protection of unclassified, PROTECTED A, and PROTECTED B information, specifying compatible modes from the SP 800-38 series.[14] This alignment is facilitated through the joint Cryptographic Module Validation Program (CMVP), operated by NIST and CCCS, which certifies hardware, software, and firmware modules implementing AES to FIPS 140-3 requirements, ensuring they meet security levels for federal procurement.[15] Validation of AES implementations emphasizes conformance to FIPS 197 through the NIST Cryptographic Algorithm Validation Program (CAVP), which generates test vectors for Known Answer Tests (KAT), Monte Carlo Tests (MCT), and Multiblock Message Tests (MMT) to verify encryption/decryption accuracy across supported modes and key sizes.[16] Successful CAVP certification is a prerequisite for CMVP module approval, confirming both algorithmic correctness and resistance to implementation flaws that could undermine security claims.[15] These processes, conducted by accredited testing laboratories, provide vendors with certificates listing validated configurations, promoting interoperable and trustworthy AES deployments.[16]Algorithm Fundamentals
High-Level Structure
The Advanced Encryption Standard (AES) is an iterative symmetric-key block cipher that processes data in fixed 128-bit blocks, using cryptographic keys of 128, 192, or 256 bits in length.[1] These key sizes correspond to AES-128, AES-192, and AES-256 variants, which employ 10, 12, and 14 rounds of transformation, respectively.[1] The algorithm was designed to provide strong security for electronic data protection while maintaining efficiency across various platforms.[1] In AES, both plaintext and ciphertext are represented as arrays of bytes, with the internal state conceptualized as a 4×4 matrix of bytes, totaling 128 bits (16 bytes arranged in 4 columns and 4 rows).[1] The encryption process begins with an initial AddRoundKey operation, where the plaintext state is combined with the first part of the expanded key using bitwise XOR.[1] This is followed by Nr−1 full rounds, each consisting of four sequential transformations: SubBytes (a nonlinear substitution), ShiftRows (a byte shifting within rows), MixColumns (a column mixing for diffusion), and AddRoundKey (another XOR with the round key).[1] The final round omits the MixColumns step, concluding with SubBytes, ShiftRows, and AddRoundKey to produce the ciphertext.[1] Decryption reverses this process by applying the inverse operations in the opposite order, starting from the final round key and proceeding backward through Nr rounds.[1] Specifically, it uses InvSubBytes (inverse substitution), InvShiftRows (inverse shifting), InvMixColumns (inverse mixing, applied in all but the first decryption round), and AddRoundKey (which remains the same due to XOR's self-inverse property).[1] The overall round structure can be visualized conceptually as a pipeline: the initial key addition sets up the state, full rounds iteratively apply substitution-permutation layers for confusion and diffusion, and the final round simplifies to avoid over-diffusion, ensuring the process is invertible with the correct key schedule.[1]Key Expansion and Schedule
The key expansion algorithm in the Advanced Encryption Standard (AES) derives a series of round keys from the initial cipher key, producing an expanded key schedule sufficient for all rounds of encryption and decryption.[1] This process begins with parameters defined by the block size and key length: the block consists of Nb = 4 words (each 32 bits, totaling 128 bits), while the cipher key length determines Nk as 4, 6, or 8 words (corresponding to 128, 192, or 256 bits) and the number of rounds Nr as 10, 12, or 14, respectively.[1] The expanded key schedule comprises Nb × (Nr + 1) words, forming a rectangular array that supplies one round key per round plus an initial round key; for example, AES-128 yields 44 words, AES-192 yields 52 words, and AES-256 yields 60 words.[1] The expansion starts by copying the Nk words of the cipher key directly into the first Nk positions of the expanded key array, denoted as w to w[Nk-1], where each word is formed from four consecutive bytes of the key.[1] Subsequent words are generated iteratively for i = Nk to Nb × (Nr + 1) - 1. A temporary word temp is set to w[i-1], then transformed based on the value of i modulo Nk to introduce nonlinearity and diffusion. Specifically, if i mod Nk = 0, temp undergoes RotWord (a cyclic left shift of its bytes by one position), followed by SubWord (byte-wise substitution using the AES S-box), and XOR with the round constant Rcon[i/Nk]; Rcon is defined as the word {rc, 00, 00, 00} in hexadecimal, where rc = (02)^{j-1} computed in the finite field GF(2^8) using the irreducible polynomial m(x) = x^8 + x^4 + x^3 + x + 1 (hexadecimal {1b}).[1] The new word is then computed as w = w[i - Nk] XOR temp.[1] This core derivation can be expressed as: for cases where i mod Nk = 0, with untransformed temp otherwise.[17] For longer keys, the process includes an additional transformation to enhance security: when Nk > 6 (i.e., AES-256 with Nk = 8) and i mod Nk = 4, temp is subjected to SubWord without rotation or round constant XOR before the final computation.[1] For AES-192 (Nk = 6), no such extra step occurs, relying solely on the periodic mod Nk = 0 transformation.[1] The following pseudocode illustrates the full algorithm:KeyExpansion(byte key[4*Nk], word w[Nb*(Nr+1)])
i = 0
while i < Nk
w[i] = (key[4*i], key[4*i+1], key[4*i+2], key[4*i+3])
i = i + 1
while i < Nb*(Nr+1)
temp = w[i-1]
if i mod Nk == 0
temp = SubWord(RotWord(temp)) XOR Rcon[i/Nk]
else if Nk > 6 and i mod Nk == 4
temp = SubWord(temp)
w[i] = w[i-Nk] XOR temp
i = i + 1
KeyExpansion(byte key[4*Nk], word w[Nb*(Nr+1)])
i = 0
while i < Nk
w[i] = (key[4*i], key[4*i+1], key[4*i+2], key[4*i+3])
i = i + 1
while i < Nb*(Nr+1)
temp = w[i-1]
if i mod Nk == 0
temp = SubWord(RotWord(temp)) XOR Rcon[i/Nk]
else if Nk > 6 and i mod Nk == 4
temp = SubWord(temp)
w[i] = w[i-Nk] XOR temp
i = i + 1
Core Transformations
SubBytes Step
The SubBytes step provides the primary source of nonlinearity and confusion in AES by substituting each byte in the 4×4 state matrix with a new byte according to a fixed substitution table known as the S-box. This transformation is applied independently to all 16 bytes of the state, ensuring an invertible nonlinear mapping that disrupts statistical relationships between plaintext and ciphertext.[1] The S-box is generated through a two-stage process: first, the input byte is replaced by its multiplicative inverse in the Galois field GF(), using the irreducible polynomial ; the zero element (byte 00) maps to itself under this inversion. Second, an affine transformation is applied over GF(2) to the inverse value: , where is a fixed 8×8 circulant matrix and is the constant 8-bit vector with hexadecimal byte value 63 (binary 01100011, assuming the least significant bit is bit 0). The matrix is defined as: [1][17] For an input byte , the -th output bit is computed as , for to 7. This design renders the S-box bijective and computationally efficient while maximizing nonlinearity to thwart linear approximations. The resulting S-box exhibits low maximum input-output correlation and small maximum differential probability, providing robust resistance to both linear and differential cryptanalysis.[1][17] Decryption requires the inverse S-box, which reverses the process by first applying the inverse affine transformation and then computing the multiplicative inverse in GF(). As an illustrative example, the S-box maps the input byte 00 (hexadecimal) to 63 (hexadecimal).[1]ShiftRows Step
The ShiftRows step in the Advanced Encryption Standard (AES) is a linear transformation that cyclically shifts the bytes within each row of the 4×4 state array to provide inter-column diffusion.[18] This step follows the SubBytes transformation in each round of the AES algorithm.[18] Specifically, the bytes in the first row (row 0) remain unchanged, while the bytes in the second row (row 1) are cyclically shifted left by one position, those in the third row (row 2) by two positions, and those in the fourth row (row 3) by three positions.[18] This arrangement ensures that each column of the output state contains bytes originally from all four columns of the input state, promoting a transposition that spreads the influence of substituted bytes horizontally across the state.[18] The transformation can be expressed mathematically as for row index to and column index to , where denotes the input state array and the output.[18] By rearranging byte positions without modifying their values, ShiftRows enhances diffusion in the cipher, ensuring that changes in a single input byte propagate to multiple output positions and contributing to the overall avalanche effect of AES.[18] For decryption, the inverse operation InvShiftRows applies cyclic right shifts to the rows: one byte for row 1, two bytes for row 2, and three bytes for row 3 (equivalently, left shifts of three, two, and one bytes, respectively), leaving row 0 unchanged.[18] Unlike other round transformations, ShiftRows has no dependency on the round key and functions solely as a fixed structural permutation.[18]MixColumns Step
The MixColumns transformation operates on the state array in the Advanced Encryption Standard (AES) by treating each of the four columns independently as elements of the finite field GF(2^8), thereby providing diffusion across the column dimension.[18] Each column is interpreted as a polynomial of degree less than 4 over GF(2^8), and the transformation multiplies this input polynomial by a fixed circulant polynomial , with the result taken modulo .[18] This linear operation ensures that each output byte in a column depends on all four input bytes, enhancing the avalanche effect essential for security.[18] Equivalently, the MixColumns step can be expressed in matrix form, where the output column is obtained by multiplying the input column vector by a predefined 4×4 matrix over GF(2^8): All multiplications and additions are performed in GF(2^8), with the irreducible polynomial (hex {11b}).[18] To implement the scalar multiplications efficiently, multiplication by 02 is computed using the xtime operation: if the most significant bit of is set, else 0), which effectively multiplies by in the field.[18] Multiplication by 03 is then , while multiplications by 01 are identities.[18] For decryption, the inverse MixColumns transformation applies the inverse matrix to reverse the mixing: This matrix corresponds to multiplication by the inverse polynomial modulo .[18] The coefficients in are precomputed values in GF(2^8), and similar xtime-based methods can optimize multiplications by 09, 0b, 0d, and 0e.[18] In the AES encryption process, MixColumns is applied in every round except the final one, where it is omitted to simplify the structure and allow direct recovery of the plaintext via XOR with the round key in the preceding AddRoundKey step.[18] This omission ensures that the final round's output remains invertible without additional linear mixing.[18]AddRoundKey Step
The AddRoundKey step in the Advanced Encryption Standard (AES) is a transformation that combines the current state—a 128-bit array arranged as a 4×4 matrix of bytes—with a round key of equal length using a bitwise exclusive-or (XOR) operation.[1] This operation applies to each byte of the state independently, where the byte at position (r, c) in the state matrix is XORed with the corresponding byte from the round key, resulting in the updated state byte s'[r, c] = s[r, c] ⊕ k[r, c], with r ranging from 0 to 3 and c from 0 to 3.[1] Equivalently, it can be viewed column-wise: each of the four 32-bit columns of the state is XORed with a 32-bit word from the round key.[1] For the initial application (prior to the first round, when round = 0), the round key consists of the first 128 bits of the cipher key (i.e., its first four 32-bit words).[1] In subsequent rounds (from 1 to the total number of rounds Nr, which is 10, 12, or 14 depending on key size), the round keys are portions of the expanded key derived from the key schedule algorithm.[1] The round key for each application matches the state size exactly, ensuring a one-to-one byte-wise combination.[1] The operation's simplicity stems from the bitwise XOR, which requires no additional tables or computations beyond the key material itself, making it highly efficient in both software and hardware implementations.[17] This XOR is inherently invertible, as applying the same operation with the identical round key yields the original state; thus, AddRoundKey serves as its own inverse during decryption, avoiding the need for a separate inverse function.[4] By integrating key material directly into the state at the beginning of each round (and at the end for the final round in encryption), it introduces key-dependent variation without altering the fundamental properties introduced by prior transformations like SubBytes, ShiftRows, or MixColumns.[17] In the broader structure of AES, AddRoundKey plays a critical role in providing key whitening, which diffuses key bits throughout the data block to enhance confusion and resistance to cryptanalytic attacks by making the intermediate states dependent on the secret key from the outset.[17] Unlike the nonlinear diffusion from steps such as MixColumns, the XOR here performs no mixing among state bytes but preserves the diffusion achieved in previous layers while ensuring each round's output is uniquely tied to the key material.[1] This design choice balances computational efficiency with security, as the operation adds no complexity beyond the key integration itself.[17] For clarity, the column-wise XOR can be expressed as: where represents words from the expanded key schedule, and for the standard AES block size.[1]Security Evaluation
Classical Cryptanalytic Attacks
The Advanced Encryption Standard (AES) has been subjected to extensive analysis using classical cryptanalytic techniques, such as differential and linear cryptanalysis, which exploit probabilistic properties of the cipher's transformations. These attacks target reduced-round versions of AES and demonstrate the robustness of the full cipher, as their complexities remain far below the exhaustive search bound of 2^128 for AES-128. Early evaluations during the AES selection process highlighted the cipher's resistance, with no practical breaks on the full number of rounds. Differential cryptanalysis, introduced by Biham and Shamir, seeks to exploit differences in plaintext pairs propagating through the cipher with predictable probabilities. For AES, the best known differential attacks apply to reduced-round variants; for instance, the attack on 7-round AES-128 requires approximately 2^{106} chosen plaintexts, as detailed in foundational work on Rijndael's vulnerabilities, which is significantly less than the 2^128 security margin of the full 10-round AES-128.[19] This approach underscores AES's design strength, where the wide-trail strategy limits differential propagation beyond a few rounds, rendering full-round attacks infeasible. Linear cryptanalysis, developed by Matsui, approximates linear relations between plaintext, ciphertext, and key bits to recover partial key information statistically. Applied to AES, the method is effective only up to 4-round versions with data complexities around 2^{40} known plaintexts, but these remain impractical for higher rounds due to the low bias of linear approximations in AES's substitution-permutation network. The cipher's nonlinear S-boxes and diffusion layers ensure that linear biases decay rapidly across multiple rounds, maintaining security well above brute-force levels.[20] More advanced techniques, such as biclique cryptanalysis introduced by Bogdanov et al., enhance meet-in-the-middle approaches by partitioning the key space into bicliques for efficient partial decryption. This method reduces the time complexity for full AES-256 to 2^254.4 encryptions using 2^8 chosen plaintexts per key group, offering only a marginal improvement over exhaustive search and posing no practical threat for 256-bit keys.[21] Similarly, related-key attacks, which assume access to encryptions under multiple related keys, yield distinguishers for reduced-round AES; for example, a 10-round AES-256 distinguisher requires 2^99.5 time and data, but such models are irrelevant to standard single-key usage scenarios where keys are secret and independent. As of 2025, AES-128 remains secure against all known classical attacks, with the strongest requiring over 2^100 operations, far exceeding practical computational resources and affirming its suitability for long-term use in the single-key model.[22] Implementations must still guard against side-channel vulnerabilities, though these fall outside classical mathematical analysis.Side-Channel Attacks
Side-channel attacks on the Advanced Encryption Standard (AES) exploit physical characteristics of implementations, such as timing variations, power consumption, electromagnetic emissions, or induced faults, rather than weaknesses in the algorithm itself. These attacks target real-world deployments where the cipher's operations leak information about the secret key through measurable side effects. Unlike classical cryptanalytic attacks, which analyze ciphertext structure for theoretical breaks, side-channel methods recover keys from implementation-specific leaks, often requiring far fewer resources in practical scenarios.[23] Timing attacks arise from non-constant-time executions in AES software implementations, particularly variable-time lookups in precomputed S-box tables or conditional branches during key expansion and round computations. For instance, if multiplication or indexing depends on key-dependent data, attackers can measure execution time differences to infer key bits, potentially recovering the full key with repeated encryptions under controlled inputs. A prominent example is cache-timing attacks, where table-based AES implementations suffer from cache contention; David A. Wagner and others demonstrated that an attacker sharing a CPU core can exploit cache eviction patterns to reveal the key, as shown in a 2005 analysis of OpenSSL's AES routine requiring only thousands of observations. Mitigations include constant-time implementations that avoid data-dependent branches and use fixed-time arithmetic, ensuring uniform execution regardless of inputs.[24] Power analysis attacks measure the device's power consumption during AES encryption to correlate it with internal operations involving the key. Simple power analysis (SPA) examines raw traces to detect round structures or key expansion phases, as the power profile varies with data processed; for example, distinct peaks from SubBytes or MixColumns steps can reveal key bytes in unmasked implementations. Differential power analysis (DPA), introduced by Paul Kocher et al., statistically processes multiple traces using models like Hamming weight or distance of intermediate values, such as the output of the first AddRoundKey step, to hypothesize key bytes and correlate against actual power data. Applied to AES, DPA can recover a full 128-bit key in approximately 2^{20} traces by targeting byte-wise hypotheses in the first round, assuming access to plaintext-ciphertext pairs. Thomas S. Messerges analyzed such vulnerabilities in AES candidates, showing how table lookups leak Hamming weight information exploitable via DPA.[25][23] Fault injection attacks deliberately induce computational errors in AES hardware or software, such as by voltage glitches, lasers, or electromagnetic pulses, then analyze the resulting faulty outputs to deduce key information. In the 2003 differential fault attack by Gilles Piret and Jean-Jacques Quisquater, faults are injected at the input to the eighth round of AES-128 (skipping the final MixColumns), producing pairs of correct and single-byte faulty ciphertexts; by exploiting the algebraic structure of the cipher, attackers solve for up to 8 bytes of the last round key using just two such pairs, then backtrack to the full key. This method targets substitution-permutation network (SPN) ciphers like AES, requiring physical access but demonstrating key recovery with minimal faults.[26] To counter these side-channel threats, AES implementations employ techniques like masking, which randomizes intermediate values by splitting them into shares (e.g., Boolean masking adds random masks to operands, hiding dependencies in power traces), blinding (multiplicative randomization of inputs to S-boxes), and threshold implementations that distribute computations across multiple shares to prevent single-point leaks. These countermeasures, such as first-order masking for AES rounds, increase computational overhead but provide probabilistic security against first-order attacks, with higher-order variants resisting multivariate analyses. The National Institute of Standards and Technology (NIST) in SP 800-57 recommends evaluating implementations for side-channel resistance, including randomized processing and secure hardware modules, to ensure key management practices mitigate physical leaks.[27]Quantum and Future Threats
The primary quantum threat to the Advanced Encryption Standard (AES) stems from Grover's algorithm, which provides a quadratic speedup for unstructured search problems, including brute-force key searches.[28] For AES with an n-bit key, this reduces the effective security from 2^n operations in the classical case to approximately 2^{n/2} quantum operations, meaning AES-128 offers only about 64 bits of quantum security while AES-256 provides 128 bits.[29] As a result, cryptographic guidelines recommend transitioning to AES-256 for applications requiring post-quantum resistance against such attacks, as it maintains a security level comparable to classical 128-bit standards.[30] Beyond Grover's algorithm, no quantum algorithms are known to provide more than a quadratic speedup for breaking the full AES cipher through key recovery or distinguishing attacks.[31] In particular, Simon's algorithm, which exploits periodic structure in functions to achieve exponential speedups, does not apply to AES due to the cipher's non-periodic key-dependent behavior in standard models.[31] This limits quantum threats to symmetric ciphers like AES primarily to search-based reductions rather than structural breaks. The National Institute of Standards and Technology (NIST) post-quantum cryptography standardization process, ongoing as of 2025, confirms that AES remains viable in the quantum era when using sufficiently large key sizes such as 256 bits.[32] AES is often integrated into hybrid schemes combining symmetric encryption with post-quantum public-key algorithms to ensure comprehensive security.[30] Future threats to AES hinge on advances in quantum hardware, particularly the development of fault-tolerant quantum computers with millions of logical qubits, which industry roadmaps project may not materialize until 2030 or later.[33] Even then, AES is not prioritized for replacement in NIST's transition plans, as its symmetric design offers straightforward mitigation through key length increases.[32] To prepare, experts advise immediate adoption of AES-256 to achieve 128-bit quantum security without disrupting existing systems.[30]Implementation Considerations
Software and Hardware Approaches
Software implementations of AES typically rely on table lookups using precomputed T-tables to accelerate the SubBytes, ShiftRows, MixColumns, and AddRoundKey operations by combining multiple transformation steps into a single lookup.[34] However, these T-table methods are susceptible to cache-timing side-channel attacks, where adversaries exploit variations in memory access times to infer intermediate values.[35] To mitigate such vulnerabilities and enable parallelism, bit-sliced implementations process multiple blocks simultaneously using bitwise operations, avoiding tables altogether and providing resistance to timing and cache-based attacks.[36] A prominent example is Intel's AES-NI instruction set, introduced in 2010 with the Westmere architecture, which includes dedicated instructions for AES rounds and offers approximately 10x performance acceleration over software-only methods on compatible processors.[34] Popular software libraries incorporate these techniques for broad applicability; for instance, OpenSSL employs T-table lookups by default but falls back to bit-sliced or integer-only code on platforms without hardware support, while also leveraging AES-NI when available.[37] Similarly, the Crypto++ library provides optimized AES implementations in C++, supporting both table-based and bitsliced variants for cross-platform use. In hardware, AES designs often use loop unrolling to pipeline the 10 or 14 rounds (depending on key length), allowing multiple blocks to be processed concurrently and increasing throughput at the cost of larger resource usage.[38] ASIC and FPGA implementations commonly employ look-up tables (LUTs) to realize the nonlinear S-box substitution, with linear operations like matrix multiplication in MixColumns handled via combinational logic for efficiency.[39] To counter side-channel attacks such as differential power analysis, dual-rail logic schemes balance power consumption across true and complementary signal paths, hiding data-dependent fluctuations, though they increase area and delay overheads.[40] FPGA vendors like AMD/Xilinx offer pre-verified AES IP cores that integrate these elements, facilitating rapid deployment in systems-on-chip.[41] Platform-specific optimizations further tailor AES to diverse environments; on mobile devices, ARM's NEON SIMD extension enables vectorized processing of multiple AES blocks in parallel using 128-bit registers, boosting efficiency for resource-constrained systems.[42] For high-volume bulk encryption, GPUs leverage massive parallelism via implementations like CUDA, distributing AES operations across thousands of threads to achieve high throughput, albeit with data transfer overheads between host and device memory.[42] Overall, software approaches prioritize flexibility and ease of integration across varying platforms but offer lower performance and heightened vulnerability to side-channel leaks compared to hardware, which delivers superior speed and security through dedicated circuitry at the expense of reconfigurability and higher development costs.[43]Performance Characteristics
The performance of the Advanced Encryption Standard (AES) varies significantly across software and hardware implementations, influenced by processor architecture, key length, and operational mode. In software implementations on modern x86 CPUs equipped with AES New Instructions (AES-NI), throughput for AES-128 encryption typically reaches 1-10 GB/s for large data streams, corresponding to approximately 0.65 cycles per byte on Intel Skylake processors. Without hardware acceleration, performance drops to 100-500 MB/s, as exemplified by benchmarks achieving around 277 MB/s on older Intel architectures using pure software routines. On ARM-based processors like the Cortex-A78, software AES-128 throughput with cryptographic extensions approximates 2 GB/s in optimized benchmarks, reflecting the core's efficiency in handling vectorized operations. Hardware implementations offer superior scalability for high-throughput applications. Application-Specific Integrated Circuits (ASICs) for AES achieve 10-100 Gbps throughput while maintaining low power consumption, such as 0.1-1 mW/Gbps in designs targeting network security, with one example delivering 12.28 Gbps at 2.56 mW total power. Field-Programmable Gate Arrays (FPGAs) provide flexible alternatives, yielding 1-10 Gbps in compact designs, though advanced pipelined configurations can exceed 20 Gbps, as seen in implementations reaching 21.56 Gbps on Xilinx Virtex devices. Latency for single-block encryption remains low: 10-20 cycles on CPUs with AES-NI due to the instruction pipeline's efficiency, and negligible (sub-cycle per block in steady state) in fully pipelined hardware setups. Comparisons across variants highlight trade-offs in speed. AES-256 is approximately 20-50% slower than AES-128 owing to its additional four rounds and expanded key schedule, with benchmarks showing a roughly 20% reduction in throughput on general-purpose CPUs. Operational modes introduce further overhead; for instance, Galois/Counter Mode (GCM) adds 10-30% computational cost over Counter (CTR) mode due to integrated authentication, though hardware-accelerated GCM mitigates this to near-parity in high-speed scenarios.| Platform | AES-128 Throughput Example | Key Metric | Source |
|---|---|---|---|
| Intel Skylake (AES-NI) | ~4.6 GB/s (at 3 GHz) | 0.65 cycles/byte | https://crypto.stanford.edu/seclab/sem-15-16/gueron.html |
| ARM Cortex-A78 (software) | ~2 GB/s | Optimized vector impl. | https://eprint.iacr.org/2025/377.pdf (contextual ARM perf.) |
| ASIC | 12.28 Gbps | 0.21 mW/Gbps | https://www.worldscientific.com/doi/pdf/10.1142/S0218126624503055 |
| FPGA (Xilinx Virtex) | 21.56 Gbps | Pipelined design | https://ieeexplore.ieee.org/abstract/document/1399176 |
Optimization Techniques
Bitslicing is a parallelization technique that processes multiple AES blocks simultaneously by rearranging data into bit-parallel representations, enabling efficient use of SIMD instructions on processors with wide registers, such as 128-bit vectors for handling up to eight blocks at once through bitwise operations like XOR and rotations. This approach transforms the byte-oriented AES operations into bit-level computations, avoiding byte-specific lookups and reducing branch dependencies for constant-time execution. For instance, on 32-bit platforms like ARM Cortex-M, bitsliced implementations achieve throughputs around 80-101 cycles per byte while processing two blocks in parallel.[44] Combined transformations optimize AES by precomputing merged operations into T-tables, which integrate the SubBytes substitution, ShiftRows permutation, and MixColumns diffusion into single lookup tables, thereby minimizing memory accesses and computational steps per round. Each T-table entry combines the Galois field multiplications (e.g., by constants 0x01, 0x02, 0x03) with the S-box affine transform, allowing a single table access followed by XOR for AddRoundKey, which contrasts with basic software table implementations that require separate lookups for each primitive. This method reduces hardware slice utilization by up to 36.5% and boosts throughput to over 57 Gbps on FPGA platforms like Virtex-2.[45] Threshold implementations provide a provably secure countermeasure against first-order side-channel attacks by decomposing AES operations, particularly the nonlinear S-box, into multiple shares using secret-sharing schemes, ensuring no single share leaks information about intermediate values without the masking overhead of higher-share randomness. The core principles include correctness (reconstructing the output), non-completeness (intermediate products independent of inputs), and uniformity (consistent share distributions), applied to AES via tower-field decompositions over GF(2^4) that use 3-5 shares per S-box computation. For AES, this results in 18% smaller hardware area and 7.5% faster execution compared to prior masked designs, with resistance demonstrated against differential power analysis using thousands of traces.[46] Fast decryption in AES employs an equivalent inverse cipher that mirrors the encryption structure, using modified inverse S-boxes to apply InvSubBytes after InvShiftRows (leveraging their commutativity) and adjusting the round key schedule with InvMixColumns for intermediate rounds, thereby avoiding computationally expensive full inverses and enabling similar performance to encryption. This approach starts with an initial AddRoundKey, followed by inverse rounds that parallel the forward cipher's sequence, culminating in a final round without InvMixColumns. As defined in the AES standard, it ensures efficient software and hardware realizations without altering the overall round count.[1] Recent advances in the 2020s include research on neural network approximations for the AES S-box, such as S-NET, which replaces the traditional lookup table with a trained feedforward network to disrupt linear correlations exploitable in side-channel attacks, though this remains experimental and non-standard due to added complexity in verification and performance trade-offs. Additionally, RISC-V instruction set extensions, like the scalar AES proposals (Zkne/Zknd), introduce dedicated instructions (e.g., saes.encsm for single-byte encryption) that accelerate AES-128 by 4-10 times over baseline T-table methods on 32/64-bit cores, with low hardware overhead of 1-8K gates, supporting all key lengths for embedded applications.[47][48]Testing and Compliance
NIST and CSEC Validation
The National Institute of Standards and Technology (NIST) oversees the Cryptographic Module Validation Program (CMVP), a joint initiative with Canada's Communications Security Establishment (CSE), to validate cryptographic modules for compliance with Federal Information Processing Standards (FIPS) 140-2 and its successor, FIPS 140-3.[15] This program ensures that modules incorporating the Advanced Encryption Standard (AES) meet rigorous security requirements, including accurate implementation of the AES algorithm for encryption and decryption across 128-, 192-, and 256-bit key lengths, as well as proper key management practices.[15] Within the CMVP framework, the Cryptographic Algorithm Validation Program (CAVP) specifically tests individual AES implementations for conformance to the AES specification in FIPS 197, using automated test suites that verify correctness in various modes such as ECB, CBC, CFB, OFB, and CTR.[16] Vendors submit their AES implementations to accredited Cryptographic and Security Testing (CST) laboratories, which run NIST-provided test vectors through the Automated Cryptographic Validation Testing System (ACVTS) to generate and evaluate results for known-answer tests (KAT) and multi-block message tests (MCT).[49] Successful validation results in a CAVP certificate, which is a prerequisite for full CMVP module certification; as of 2025, thousands of AES algorithm certificates have been issued, supporting widespread adoption in government and commercial systems.[49] Certificates are publicly listed and remain valid until superseded by standard updates or identified flaws, with the overall CMVP maintaining an active list of validated modules that often include certified AES components.[50] The CSE contributes to the CMVP and CAVP as a co-manager, ensuring the validation process aligns with Canadian government security needs under the Communications Security Establishment (CSE) guidelines, which mirror NIST standards but emphasize interoperability for binational use cases such as PROTECTED information handling. This equivalence allows CSE-validated modules to be recognized equivalently to NIST validations, facilitating cross-border compliance without redundant testing.[51] Revocations of validated modules are infrequent but occur when fundamental flaws are discovered, such as the 2013-2014 withdrawal of the Dual_EC_DRBG pseudorandom number generator from NIST SP 800-90A due to security concerns, which led to the revocation or revalidation of affected FIPS modules that relied on it for entropy in AES key generation.[52] In such cases, NIST and CSE issue announcements requiring vendors to update or remove the flawed components to maintain certification status.Standard Test Vectors
Standard test vectors for the Advanced Encryption Standard (AES) are predefined inputs and expected outputs provided by authoritative standards to verify the correctness of implementations. These vectors ensure that AES algorithms produce identical results across different systems, helping to detect errors such as incorrect S-box implementations, endianness issues, or flaws in the key expansion process.[1][16] The primary source of test vectors is Appendix B of NIST FIPS 197, which includes examples for AES in Electronic Codebook (ECB) mode across all key sizes (128, 192, and 256 bits), along with intermediate values during encryption and decryption for detailed validation. These vectors cover full encryption and partial decryption intermediates to confirm step-by-step compliance. Developers use these to self-validate implementations prior to submission for formal certification under the Cryptographic Module Validation Program (CMVP).[1] For AES-128 in ECB mode, a representative vector is:- Key:
000102030405060708090a0b0c0d0e0f - Plaintext:
00112233445566778899aabbccddeeff - Ciphertext:
69c4e0d86a7b0430d8cdb78070b4c55a
- Key:
000102030405060708090a0b0c0d0e0f1011121314151617 - Plaintext:
00112233445566778899aabbccddeeff - Ciphertext:
dda97ca4864cdfe06eaf70a0ec0d7191
- Key:
000102030405060708090a0b0c0d0e0f101112131415161718191a1b1c1d1e1f - Plaintext:
00112233445566778899aabbccddeeff - Ciphertext:
8ea2b7ca516745bfeafc49904b496089
- Key:
2b7e151628aed2a6abf7158809cf4f3c - Plaintext:
3243f6a8885a308d313198a2e0370734 - Ciphertext:
39202dc1925dc11a6a9f0b6d1052ed05
| Key | IV | Plaintext | Ciphertext |
|---|---|---|---|
2b7e151628aed2a6abf7158809cf4f3c | 000102030405060708090a0b0c0d0e0f | 6bc1bee22e409f96e93d7e117393172a | 7649abac8119b246cee98e9b12e9197d |
- Key:
06a9214036b8a15b512e03d534120006 - IV:
3dafba429d9eb430b422da802c9fac41 - Plaintext:
"Single block msg"(ASCII) - Ciphertext:
e353779c1079aeb82708942dbe77181a
_Round_Function.png/250px-AES_(Rijndael)_Round_Function.png)
_Round_Function.png)












![{\displaystyle \operatorname {GF} (2)[x]}](https://wikimedia.org/api/rest_v1/media/math/render/svg/6334bd0b6ddc3a60f9d7590f71c74e11f780b80f)

