Recent from talks
Nothing was collected or created yet.
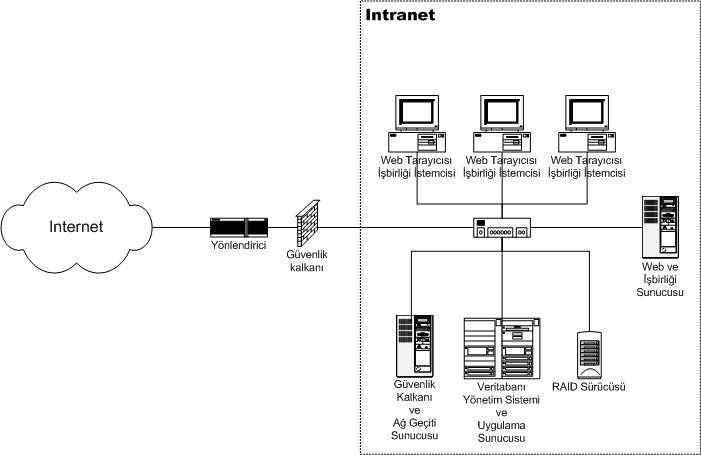
Intranet
View on WikipediaThis article is written like a personal reflection, personal essay, or argumentative essay that states a Wikipedia editor's personal feelings or presents an original argument about a topic. (July 2023) |

An intranet is a computer network for sharing information, easier communication, collaboration tools, operational systems, and other computing services within an organization, usually to the exclusion of access by outsiders.[1] The term is used in contrast to public networks, such as the Internet, but uses the same technology based on the Internet protocol suite.[2]
An organization-wide intranet can constitute an important focal point of internal communication and collaboration, and provide a single starting point to access internal and external resources. In its simplest form, an intranet is established with the technologies for local area networks (LANs) and wide area networks (WANs).[3][4][5] Many modern intranets have search engines, user profiles, blogs, mobile apps with notifications, and events planning within their infrastructure.
An intranet is sometimes contrasted to an extranet. While an intranet is generally restricted to employees of the organization, extranets may also be accessed by customers, suppliers, or other approved parties.[6] Extranets extend a private network onto the Internet with special provisions for authentication, authorization and accounting (AAA protocol).
Uses
[edit]Intranets are increasingly being used to deliver tools, such as for collaboration (to facilitate working in groups and teleconferencing) or corporate directories, sales and customer relationship management, or project management. Intranets are also used as corporate culture-change platforms. For example, a large number of employees using an intranet forum application to host a discussion about key issues could come up with new ideas related to management, productivity, quality, and other corporate issues. In large intranets, website traffic is often similar to public website traffic and can be better understood by using web metrics software to track overall activity. User surveys also improve intranet website effectiveness.
Larger businesses allow users within their intranet to access public internet through firewall servers. They have the ability to screen incoming and outgoing messages, keeping security intact. When part of an intranet is made accessible to customers and others outside the business, it becomes part of an extranet. Businesses can send private messages through the public network using special encryption/decryption and other security safeguards to connect one part of their intranet to another.
Intranet user-experience, editorial, and technology teams work together to produce in-house sites. Most commonly, intranets are managed by the communications, HR or CIO departments of large organizations, or some combination of these.
Because of the scope and variety of content and the number of system interfaces, the intranets of many organizations are much more complex than their respective public websites. Intranets and the use of intranets are growing rapidly. According to the Intranet Design Annual 2007 from Nielsen Norman Group, the number of pages on participants' intranets averaged 200,000 over the years 2001 to 2003 and has grown to an average of 6 million pages over 2005–2007.[7]
Benefits
[edit]This section may require cleanup to meet Wikipedia's quality standards. The specific problem is: Several paragraphs can be summed up as "Intranets allow users to access and/or interact with information", potentially making them appear redundant. (January 2025) |
Intranets can help users locate and view information faster and use applications relevant to their roles and responsibilities. With a web browser interface, users can access data held in any database the organization wants to make available at any time and — subject to security provisions — from anywhere within company workstations, increasing employees' ability to perform their jobs faster, more accurately, and with confidence that they have the right information. It also helps improve services provided to users.
Using hypermedia and Web technology, Web publishing allows for the maintenance of and easy access to cumbersome corporate knowledge, such as employee manuals, benefits documents, company policies, business standards, news feeds, and even training, all of which can be accessed throughout a company using common Internet standards (Acrobat files, Flash files, CGI applications). Because each business unit can update the online copy of a document, the most recent version is usually available to employees using the intranet. Intranets are also used as a platform for developing and deploying applications to support business operations and decisions across the internetworked enterprise.
Information is easily accessible to all authorised users, enabling collaboration. Being able to communicate in real-time through integrated third-party tools, such as an instant messenger, promotes the sharing of ideas and removes blockages to communication to help boost a business's productivity.[citation needed]
Intranets can serve as powerful tools for communicating (such as through chat, email and/or blogs) within a given organization about vertically strategic initiatives that have a global reach throughout said organization. The type of information that can easily be conveyed is the purpose of the initiative and what it is aiming to achieve, who is driving it, results achieved to date, and whom to speak to for more information. By providing this information on the intranet, staff can keep up-to-date with the strategic focus of their organization. For example, when Nestlé had a number of food processing plants in Scandinavia, their central support system had to deal with a number of queries every day.[8] When Nestlé decided to invest in an intranet, they quickly realized the savings. Gerry McGovern says that the savings from the reduction in query calls was substantially greater than the investment in the intranet.
Users can view information and data via a web browser rather than maintaining physical documents such as procedure manuals, internal phone list and requisition forms. This can potentially save the business money on printing, duplicating documents, and the environment, as well as document maintenance overhead. For example, the HRM company PeopleSoft "derived significant cost savings by shifting HR processes to the intranet".[8] McGovern goes on to say the manual cost of enrolling in benefits was found to be US$109.48 per enrollment. "Shifting this process to the intranet reduced the cost per enrollment to $21.79; a saving of 80 percent". Another company that saved money on expense reports was Cisco. "In 1996, Cisco processed 54,000 reports and the amount of dollars processed was USD19 million".[8]
Many companies dictate computer specifications which, in turn, may allow Intranet developers to write applications that only have to work on one browser such that there are no cross-browser compatibility issues. Being able to specifically address one's "viewer" is a great advantage. Since intranets are user-specific (requiring database/network authentication prior to access), users know exactly who they are interfacing with and can personalize their intranet based on role (job title, department) or individual ("Congratulations Jane, on your 3rd year with our company!").
Since "involvement in decision making" is one of the main drivers of employee engagement,[9] offering tools (like forums or surveys) that foster peer-to-peer collaboration and employee participation can make employees feel more valued and involved.
Planning and creation
[edit]Most organizations devote considerable resources into the planning and implementation of their intranet as it is of strategic importance to the organization's success. Some of the planning would include topics such as determining the purpose and goals of the intranet,[10][11] identifying persons or departments responsible for implementation and management and devising functional plans, page layouts and designs.
The appropriate staff would also ensure that implementation schedules and phase-out of existing systems were organized, while defining and implementing security of the intranet and ensuring it lies within legal boundaries and other constraints. In order to produce a high-value end product, systems planners should determine the level of interactivity (e.g. wikis, on-line forms) desired.
Planners may also consider whether the input of new data and updating of existing data is to be centrally controlled or devolve. These decisions sit alongside to the hardware and software considerations (like content management systems), participation issues (like good taste, harassment, confidentiality), and features to be supported.[12]
Intranets are often static sites; they are a shared drive, serving up centrally stored documents alongside internal articles or communications (often one-way communication). By leveraging firms which specialise in 'social' intranets, organisations are beginning to think of how their intranets can become a 'communication hub' for their entire team. The actual implementation would include steps such as securing senior management support and funding,[13] conducting a business requirement analysis and identifying users' information needs.
From the technical perspective, there would need to be a coordinated installation of the web server and user access network, the required user/client applications and the creation of document framework (or template) for the content to be hosted.[14]
The end-user should be involved in testing and promoting use of the company intranet, possibly through a parallel adoption methodology or pilot programme. In the long term, the company should carry out ongoing measurement and evaluation, including through benchmarking against other company services.[15][16]
Maintenance
[edit]Some aspects are non-static.
Staying current
[edit]An intranet structure needs key personnel committed to maintaining the intranet and keeping content current. For feedback on the intranet, social networking can be done through a forum for users to indicate what they want and what they do not like.
Privacy protection
[edit]The European Union's General Data Protection Regulation went into effect May 2018. Since then, the protection of the privacy of employees, customers and other stakeholders (e.g. consultants) has become more and more a significant concern for most companies (at least, all those having an interest in markets and countries where regulations are in place to protect the privacy).
Enterprise private network
[edit]An enterprise private network is a computer network built by a business to interconnect its various company sites (such as production sites, offices and shops) in order to share computer resources.
Beginning with the digitalisation of telecommunication networks, started in the 1970s in the US by AT&T,[17] and propelled by the growth in computer systems availability and demands, enterprise networks have been built for decades without the need to append the term private to them. The networks were operated over telecommunications networks and, as for voice communications, a certain amount of security and secrecy was expected and delivered.
But with the Internet in the 1990s came a new type of network, virtual private networks, built over this public infrastructure, using encryption to protect the data traffic from eaves-dropping. So the enterprise networks are now commonly referred to as enterprise private networks in order to clarify that these are private networks, in contrast to public networks.
See also
[edit]References
[edit]- ^ Scott, Judy E. "Organizational knowledge and the intranet". Decision Support Systems.
- ^ "The Difference Between Internet, Intranet, and Extranet", October 19, 1998, Steven L. Telleen, http://www.iorg.com/
- ^ Luk, A. (9 May 1991). "Fujikama goes Unix". [1991] IEEE Pacific Rim Conference on Communications, Computers and Signal Processing Conference Proceedings. Vol. 2. Institute of Electrical and Electronics Engineers. pp. 783–786. doi:10.1109/PACRIM.1991.160857. ISBN 978-0879426385. S2CID 61487882.
The internet and intranet Unix network provide a functioning email facility around the world.
- ^ Richardson, C.; Schoultz, M. (14 October 1991). "Formation flight system design concept". IEEE/AIAA 10th Digital Avionics Systems Conference. pp. 18–25. doi:10.1109/DASC.1991.177138. S2CID 110893057.
The data transfer task is broken up into two network solutions: an intranet used for transferring data among formation members at high update rates to support close formation flight and an internet used for transferring data among the separate formations at lower update rates.
- ^ RFC 4364
- ^ Callaghan, J (2002). Inside Intranets & Extranets: Knowledge Management AND the Struggle for Power. Palgrave Macmillan. ISBN 0-333-98743-8.
- ^ Pernice Coyne, Kara; Schwartz, Mathew; Nielsen, Jakob (2007), "Intranet Design Annual 2007", Nielsen Norman Group
- ^ a b c McGovern, Gerry (November 18, 2002). "Intranet return on investment case studies". Archived from the original on April 6, 2009. Retrieved 2009-04-03.
- ^ "Report Summary: The drivers of employee engagement | Institute for Employment Studies". Report Summary: The drivers of employee engagement | Institute for Employment Studies. Retrieved 2018-01-04.
- ^ Wright, Andrew. "8 good business reasons for having an intranet". Archived from the original on 2 February 2014. Retrieved 3 September 2013.
- ^ Wright, Andrew. "From innovation to operation: the role of the intranet". Archived from the original on 2 February 2014. Retrieved 3 September 2013.
- ^ LaMee, James A. (2002-04-30). "Intranets and Special Libraries: Making the most of inhouse communications". University of South Carolina. Archived from the original on 2009-02-18. Retrieved 2009-04-03.
- ^ Ward, Toby. "Planning: An Intranet Model for success Intranet". Archived from the original on 2009-03-22. Retrieved 2009-04-03.
- ^ Intranet: Table of Contents – Macmillan Computer Sciences: Internet and Beyond. Bookrags.com. Retrieved 2009-04-03.
- ^ "Intranet benchmarking explained". Intranet Benchmarking Forum. Archived from the original on 2011-07-13. Retrieved 2009-04-03.
- ^ "Benchmarking intranet end user satisfaction". Archived from the original on 2013-09-30. Retrieved 2013-09-03.
- ^ "History of network switching". AT&T.