Network theory
View on Wikipedia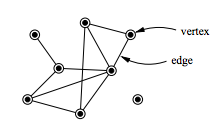
| Part of a series on | ||||
| Network science | ||||
|---|---|---|---|---|
| Network types | ||||
| Graphs | ||||
|
||||
| Models | ||||
|
||||
| ||||
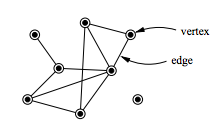
In mathematics, computer science, and network science, network theory is a part of graph theory. It defines networks as graphs where the vertices or edges possess attributes. Network theory analyses these networks over the symmetric relations or asymmetric relations between their (discrete) components.
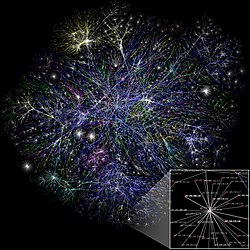
Network theory has applications in many disciplines, including statistical physics, particle physics, computer science, electrical engineering,[1][2] biology,[3] archaeology,[4] linguistics,[5][6][7] economics[8], finance, operations research, climatology, ecology, public health,[9][10][11] sociology,[12] psychology,[13] and neuroscience.[14][15][16] Applications of network theory include logistical networks, the World Wide Web, Internet, gene regulatory networks, metabolic networks, social networks, epistemological networks, etc.; see List of network theory topics for more examples.
Euler's solution of the Seven Bridges of Königsberg problem is considered to be the first true proof in the theory of networks.
Network optimization
[edit]Network problems that involve finding an optimal way of doing something are studied as combinatorial optimization. Examples include network flow, shortest path problem, transport problem, transshipment problem, location problem, matching problem, assignment problem, packing problem, routing problem, critical path analysis, and program evaluation and review technique.
Network analysis
[edit]Electric network analysis
[edit]The analysis of electric power systems could be conducted using network theory from two main points of view:
- An abstract perspective (i.e., as a graph consists from nodes and edges), regardless of the electric power aspects (e.g., transmission line impedances). Most of these studies focus only on the abstract structure of the power grid using node degree distribution and betweenness distribution, which introduces substantial insight regarding the vulnerability assessment of the grid. Through these types of studies, the category of the grid structure could be identified from the complex network perspective (e.g., single-scale, scale-free). This classification might help the electric power system engineers in the planning stage or while upgrading the infrastructure (e.g., add a new transmission line) to maintain a proper redundancy level in the transmission system.[1]
- Weighted graphs that blend an abstract understanding of complex network theories and electric power systems properties.[2]
Social network analysis
[edit]
Social network analysis examines the structure of relationships between social entities.[18] These entities are often persons, but may also be groups, organizations, nation states, web sites, or scholarly publications.
Since the 1970s, the empirical study of networks has played a central role in social science, and many of the mathematical and statistical tools used for studying networks have been first developed in sociology.[19] Amongst many other applications, social network analysis has been used to understand the diffusion of innovations, news and rumors.[20] Similarly, it has been used to examine the spread of both diseases and health-related behaviors.[21] It has also been applied to the study of markets, where it has been used to examine the role of trust in exchange relationships and of social mechanisms in setting prices.[22] It has been used to study recruitment into political movements, armed groups, and other social organizations.[23] It has also been used to conceptualize scientific disagreements[24] as well as academic prestige.[25] More recently, network analysis (and its close cousin traffic analysis) has gained a significant use in military intelligence,[26] for uncovering insurgent networks of both hierarchical and leaderless nature.[citation needed]
Biological network analysis
[edit]With the recent explosion of publicly available high throughput biological data, the analysis of molecular networks has gained significant interest.[27] The type of analysis in this context is closely related to social network analysis, but often focusing on local patterns in the network. For example, network motifs are small subgraphs that are over-represented in the network. Similarly, activity motifs are patterns in the attributes of nodes and edges in the network that are over-represented given the network structure. Using networks to analyze patterns in biological systems, such as food-webs, allows us to visualize the nature and strength of interactions between species. The analysis of biological networks with respect to diseases has led to the development of the field of network medicine.[28] Recent examples of application of network theory in biology include applications to understanding the cell cycle[29] as well as a quantitative framework for developmental processes.[30]
Narrative network analysis
[edit]
The automatic parsing of textual corpora has enabled the extraction of actors and their relational networks on a vast scale. The resulting narrative networks, which can contain thousands of nodes, are then analyzed by using tools from Network theory to identify the key actors, the key communities or parties, and general properties such as robustness or structural stability of the overall network, or centrality of certain nodes.[32] This automates the approach introduced by Quantitative Narrative Analysis,[33] whereby subject-verb-object triplets are identified with pairs of actors linked by an action, or pairs formed by actor-object.[31]
Link analysis
[edit]Link analysis is a subset of network analysis, exploring associations between objects. An example may be examining the addresses of suspects and victims, the telephone numbers they have dialed, and financial transactions that they have partaken in during a given timeframe, and the familial relationships between these subjects as a part of police investigation. Link analysis here provides the crucial relationships and associations between very many objects of different types that are not apparent from isolated pieces of information. Computer-assisted or fully automatic computer-based link analysis is increasingly employed by banks and insurance agencies in fraud detection, by telecommunication operators in telecommunication network analysis, by medical sector in epidemiology and pharmacology, in law enforcement investigations, by search engines for relevance rating (and conversely by the spammers for spamdexing and by business owners for search engine optimization), and everywhere else where relationships between many objects have to be analyzed. Links are also derived from similarity of time behavior in both nodes. Examples include climate networks where the links between two locations (nodes) are determined, for example, by the similarity of the rainfall or temperature fluctuations in both sites.[34][35]
Web link analysis
[edit]Several Web search ranking algorithms use link-based centrality metrics, including Google's PageRank, Kleinberg's HITS algorithm, the CheiRank and TrustRank algorithms. Link analysis is also conducted in information science and communication science in order to understand and extract information from the structure of collections of web pages. For example, the analysis might be of the interlinking between politicians' websites or blogs. Another use is for classifying pages according to their mention in other pages.[36]
Centrality measures
[edit]Information about the relative importance of nodes and edges in a graph can be obtained through centrality measures, widely used in disciplines like sociology. For example, eigenvector centrality uses the eigenvectors of the adjacency matrix corresponding to a network, to determine nodes that tend to be frequently visited. Formally established measures of centrality are degree centrality, closeness centrality, betweenness centrality, eigenvector centrality, subgraph centrality, and Katz centrality. The purpose or objective of analysis generally determines the type of centrality measure to be used. For example, if one is interested in dynamics on networks or the robustness of a network to node/link removal, often the dynamical importance[37] of a node is the most relevant centrality measure.
Assortative and disassortative mixing
[edit]These concepts are used to characterize the linking preferences of hubs in a network. Hubs are nodes which have a large number of links. Some hubs tend to link to other hubs while others avoid connecting to hubs and prefer to connect to nodes with low connectivity. We say a hub is assortative when it tends to connect to other hubs. A disassortative hub avoids connecting to other hubs. If hubs have connections with the expected random probabilities, they are said to be neutral. There are three methods to quantify degree correlations.[38]
Recurrence networks
[edit]The recurrence matrix of a recurrence plot can be considered as the adjacency matrix of an undirected and unweighted network. This allows for the analysis of time series by network measures. Applications range from detection of regime changes over characterizing dynamics to synchronization analysis.[39][40][41]
Spatial networks
[edit]Many real networks are embedded in space. Examples include, transportation and other infrastructure networks, brain neural networks. Several models for spatial networks have been developed.[42]
Temporal networks
[edit]Other networks emphasise the evolution over time of systems of nodes and their interconnections. Temporal networks are used for example to study how financial risk has spread across countries.[43] In this study, temporal networks are used to also visually trace the intricate dynamics of financial contagion during crises. Unlike traditional network approaches that aggregate or analyze static snapshots, the study uses a time-respecting path methodology to preserve the sequence and timing of financial crises contagion events. This enables the identification of nodes as sources, transmitters, or receivers of financial stress, avoiding mischaracterizations inherent in static or aggregated methods. Following this approach, banks are found to serve as key intermediaries in contagion paths, and temporal analysis pinpoints smaller countries like Greece and Italy as significant origins of shocks during crises—insights obscured by static approaches that overemphasize large economies like the US or Japan.
Temporal networks can also be used to explore how cooperation evolves in dynamic, real-world population structures where interactions are time-dependent.[44] Here the authors find that network temporality enhances cooperation compared to static networks, even though "bursty" interaction patterns typically hinder it. This finding also shows how cooperation and other emergent behaviours can thrive in realistic, time-varying population structures, challenging conventional assumptions rooted in static models.
In psychology, temporal networks enable the understanding of psychological disorders by framing them as dynamic systems of interconnected symptoms rather than outcomes of a single underlying cause. Using "nodes" to represent symptoms and "edges" to signify their direct interactions, symptoms like insomnia and fatigue are shown how they influence each other over time; also, disorders such as depression are shown not to be fixed entities but evolving networks, where identifying "bridge symptoms" like concentration difficulties can explain comorbidity between conditions such as depression and anxiety.[45]
Lastly, temporal networks enable a better understanding and controlling of the spread of infectious diseases.[46] Unlike traditional static networks, which assume continuous, unchanging connections, temporal networks account for the precise timing and duration of interactions between individuals. This dynamic approach reveals critical nuances, such as how diseases can spread via time-sensitive pathways that static models miss. Temporal data, such as interactions captured through Bluetooth sensors or in hospital wards, can improve predictions of outbreak speed and extent. Overlooking temporal correlations can lead to significant errors in estimating epidemic dynamics, emphasizing the need for a temporal framework to develop more accurate strategies for disease control.
Spread
[edit]Content in a complex network can spread via two major methods: conserved spread and non-conserved spread.[47] In conserved spread, the total amount of content that enters a complex network remains constant as it passes through. The model of conserved spread can best be represented by a pitcher containing a fixed amount of water being poured into a series of funnels connected by tubes. Here, the pitcher represents the original source and the water is the content being spread. The funnels and connecting tubing represent the nodes and the connections between nodes, respectively. As the water passes from one funnel into another, the water disappears instantly from the funnel that was previously exposed to the water. In non-conserved spread, the amount of content changes as it enters and passes through a complex network. The model of non-conserved spread can best be represented by a continuously running faucet running through a series of funnels connected by tubes. Here, the amount of water from the original source is infinite. Also, any funnels that have been exposed to the water continue to experience the water even as it passes into successive funnels. The non-conserved model is the most suitable for explaining the transmission of most infectious diseases, neural excitation, information and rumors, etc.
Network immunization
[edit]The question of how to immunize efficiently scale free networks which represent realistic networks such as the Internet and social networks has been studied extensively. One such strategy is to immunize the largest degree nodes, i.e., targeted (intentional) attacks[48] since for this case is relatively high and fewer nodes are needed to be immunized. However, in most realistic networks the global structure is not available and the largest degree nodes are unknown.
See also
[edit]- Actor-network theory
- Complex network
- Complex system
- Systems thinking
- Congestion game
- Quantum complex network
- Dual-phase evolution
- Network partition
- Network science
- Network theory in risk assessment
- Network topology
- Network analyzer
- Seven Bridges of Königsberg
- Small-world networks
- Social network
- Scale-free networks
- Network dynamics
- Sequential dynamical systems
- Pathfinder networks
- Human disease network
- Biological network
- Network medicine
- Graph partition
References
[edit]- ^ a b Borchers A, Pieler T (November 2010). "Programming pluripotent precursor cells derived from Xenopus embryos to generate specific tissues and organs". Genes. 1 (3): 413–426. doi:10.3390/en11061381. PMC 3966229. PMID 24710095.
- ^ a b Saleh, Mahmoud; Esa, Yusef; Onuorah, Nwabueze; Mohamed, Ahmed A. (2017). "Optimal microgrids placement in electric distribution systems using complex network framework". Optimal microgrids placement in electric distribution systems using complex network framework - IEEE Conference Publication. IEEE. pp. 1036–1040. doi:10.1109/ICRERA.2017.8191215. ISBN 978-1-5386-2095-3. S2CID 44685630. Archived from the original on 2020-03-06. Retrieved 2018-06-07.
- ^ Habibi I, Emamian ES, Abdi A (August 2014). "Quantitative analysis of intracellular communication and signaling errors in signaling networks". BMC Systems Biology. 8 89. doi:10.1186/s12918-014-0089-z. PMC 4255782. PMID 25115405.
- ^ Sindbæk S (2007). Networks and nodal points: the emergence of towns in early Viking Age Scandinavia - Antiquity 81(311). Cambridge University Press. pp. 119–132.
- ^ Paradowski, M. B.; Jarynowski, A.; Jelińska, M.; Czopek, K. (2021). "Selected poster presentations from the American Association of Applied Linguistics conference, Denver, USA, March 2020: Out-of-class peer interactions matter for second language acquisition during short-term overseas sojourns: The contributions of Social Network Analysis". Language Teaching. 54 (1): 139–143. doi:10.1017/S0261444820000580.
- ^ Paradowski, M. B.; Jarynowski, A.; Czopek, K.; Jelińska, M.; et al. (2021). "Peer interactions and second language learning: The contributions of Social Network Analysis in Study Abroad vs At-Home environments". In Mitchell, Rosamond; Tyne, Henry (eds.). Language, Mobility and Study Abroad in the Contemporary European Context. New York: Routledge. pp. 99–116. doi:10.1017/S0261444820000580. ISBN 978-10-03087-95-3. S2CID 228863564.
- ^ Paradowski, M. B.; Cierpich-Kozieł, A.; Chen, C.-C.; Ochab, J. K. (2022). "How output outweighs input and interlocutors matter for study-abroad SLA: Computational Social Network Analysis of learner interactions". The Modern Language Journal. 106 (4): 694–725. doi:10.1111/modl.12811. S2CID 255247273. Archived from the original on 2023-01-06. Retrieved 2023-08-26.
- ^ Zinilli, Antonio; Gao, Yang; Scherngell, Thomas (2024). "Structural Dynamics of Inter-city Innovation Networks in China: A Perspective From TERGM". Networks and Spatial Economics. 24 (3): 707–741. doi:10.1007/s11067-024-09634-2.
- ^ Harris JK, Luke DA, Zuckerman RB, Shelton SC (June 2009). "Forty years of secondhand smoke research: the gap between discovery and delivery". American Journal of Preventive Medicine. 36 (6): 538–548. doi:10.1016/j.amepre.2009.01.039. OCLC 5899755895. PMID 19372026.
- ^ Varda DM, Forgette R, Banks D, Contractor N (2009). "Social Network Methodology in the Study of Disasters: Issues and Insights Prompted by Post-Katrina Research". Population Research and Policy Review. 28 (1): 11–29. doi:10.1007/s11113-008-9110-9. ISSN 0167-5923. OCLC 5659930640. S2CID 144130904.
- ^ Sunkersing D, Martin FC, Sullivan P, Bell D (December 2022). "Care and support networks of community-dwelling frail individuals in North West London: a comparison of patient and healthcare workers' perceptions". BMC Geriatrics. 22 (1) 953. doi:10.1186/s12877-022-03561-y. PMC 9737751. PMID 36494627.
- ^ della Porta D, Diani M (2010). Social Movements 2e: An Introduction (2nd ed.). Wiley-Blackwell. ISBN 978-1-4051-0282-7.
- ^ Paradowski, M. B.; Jelińska, M. (2023). "The predictors of L2 grit and their complex interactions in online foreign language learning: Motivation, self-directed learning, autonomy, curiosity, and language mindsets". Computer Assisted Language Learning. 37 (8): 2320–2358. doi:10.1080/09588221.2023.2192762.
- ^ Bassett DS, Sporns O (February 2017). "Network neuroscience". Nature Neuroscience. 20 (3): 353–364. doi:10.1038/nn.4502. PMC 5485642. PMID 28230844.
- ^ Alex Fornito. "An Introduction to Network Neuroscience: How to build, model, and analyse connectomes - 0800-10:00 | OHBM". pathlms.com. Archived from the original on 2023-02-04. Retrieved 2020-03-11.
- ^ Saberi M, Khosrowabadi R, Khatibi A, Misic B, Jafari G (January 2021). "Topological impact of negative links on the stability of resting-state brain network". Scientific Reports. 11 (1) 2176. Bibcode:2021NatSR..11.2176S. doi:10.1038/s41598-021-81767-7. PMC 7838299. PMID 33500525.
- ^ Grandjean M (2014). "La connaissance est un réseau". Les Cahiers du Numérique. 10 (3): 37–54. doi:10.3166/lcn.10.3.37-54. Retrieved 2014-10-15.
- ^ Wasserman, Stanley and Katherine Faust. 1994. Social Network Analysis: Methods and Applications. Cambridge: Cambridge University Press. Rainie, Lee and Barry Wellman, Networked: The New Social Operating System. Cambridge, MA: MIT Press, 2012.
- ^ Newman, M.E.J. Networks: An Introduction. Oxford University Press. 2010
- ^ Al-Taie MZ, Kadry S (2017). "Information Diffusion in Social Networks". Python for Graph and Network Analysis. Advanced Information and Knowledge Processing. pp. 165–184. doi:10.1007/978-3-319-53004-8_8. ISBN 978-3-319-53003-1. PMC 7123536.
- ^ Luke DA, Harris JK (April 2007). "Network analysis in public health: history, methods, and applications". Annual Review of Public Health. 28 (1): 69–93. doi:10.1146/annurev.publhealth.28.021406.144132. PMID 17222078.
- ^ Odabaş M, Holt TJ, Breiger RL (October 2017). "Markets as Governance Environments for Organizations at the Edge of Illegality: Insights From Social Network Analysis". American Behavioral Scientist. 61 (11): 1267–1288. doi:10.1177/0002764217734266. hdl:10150/631238. S2CID 158776581.
- ^ Larson JM (11 May 2021). "Networks of Conflict and Cooperation". Annual Review of Political Science. 24 (1): 89–107. doi:10.1146/annurev-polisci-041719-102523.
- ^ Leng RI (24 May 2018). "A network analysis of the propagation of evidence regarding the effectiveness of fat-controlled diets in the secondary prevention of coronary heart disease (CHD): Selective citation in reviews". PLOS ONE. 13 (5) e0197716. Bibcode:2018PLoSO..1397716L. doi:10.1371/journal.pone.0197716. PMC 5968408. PMID 29795624.
- ^ Burris V (April 2004). "The Academic Caste System: Prestige Hierarchies in PhD Exchange Networks". American Sociological Review. 69 (2): 239–264. doi:10.1177/000312240406900205. S2CID 143724478. Archived from the original on 15 May 2021. Retrieved 22 September 2021.
- ^ Roberts N, Everton SF. "Strategies for Combating Dark Networks" (PDF). Journal of Social Structure. 12. Archived (PDF) from the original on 17 October 2021. Retrieved 22 September 2021.
- ^ Habibi I, Emamian ES, Abdi A (2014-10-07). "Advanced fault diagnosis methods in molecular networks". PLOS ONE. 9 (10) e108830. Bibcode:2014PLoSO...9j8830H. doi:10.1371/journal.pone.0108830. PMC 4188586. PMID 25290670.
- ^ Barabási AL, Gulbahce N, Loscalzo J (January 2011). "Network medicine: a network-based approach to human disease". Nature Reviews. Genetics. 12 (1): 56–68. doi:10.1038/nrg2918. PMC 3140052. PMID 21164525.
- ^ Jailkhani N, Ravichandran S, Hegde SR, Siddiqui Z, Mande SC, Rao KV (December 2011). "Delineation of key regulatory elements identifies points of vulnerability in the mitogen-activated signaling network". Genome Research. 21 (12): 2067–2081. doi:10.1101/gr.116145.110. PMC 3227097. PMID 21865350.
- ^ Jackson MD, Duran-Nebreda S, Bassel GW (October 2017). "Network-based approaches to quantify multicellular development". Journal of the Royal Society, Interface. 14 (135) 20170484. doi:10.1098/rsif.2017.0484. PMC 5665831. PMID 29021161.
- ^ a b Sudhahar, Saatviga; Veltri, Giuseppe A; Cristianini, Nello (2015). "Automated analysis of the US presidential elections using Big Data and network analysis". Big Data & Society. 2 (1): 205395171557291. doi:10.1177/2053951715572916. hdl:2381/31767.
- ^ Network analysis of narrative content in large corpora Archived 2021-06-24 at the Wayback Machine; S Sudhahar, G De Fazio, R Franzosi, N Cristianini; Natural Language Engineering, 1–32, 2013
- ^ Quantitative Narrative Analysis; Roberto Franzosi; Emory University © 2010
- ^ Tsonis AA, Swanson KL, Roebber PJ (2006). "What Do Networks Have to Do with Climate?". Bulletin of the American Meteorological Society. 87 (5): 585–595. Bibcode:2006BAMS...87..585T. doi:10.1175/BAMS-87-5-585. ISSN 0003-0007.
- ^ Boers N, Bookhagen B, Barbosa HM, Marwan N, Kurths J, Marengo JA (October 2014). "Prediction of extreme floods in the eastern Central Andes based on a complex networks approach". Nature Communications. 5 5199. Bibcode:2014NatCo...5.5199B. doi:10.1038/ncomms6199. PMID 25310906. S2CID 3032237.
- ^ Attardi G, Di Marco S, Salvi D (1998). "Categorization by Context" (PDF). Journal of Universal Computer Science. 4 (9): 719–736. Archived (PDF) from the original on 2020-10-25. Retrieved 2012-09-07.
- ^ Restrepo JG, Ott E, Hunt BR (September 2006). "Characterizing the dynamical importance of network nodes and links". Physical Review Letters. 97 (9) 094102. arXiv:cond-mat/0606122. Bibcode:2006PhRvL..97i4102R. doi:10.1103/PhysRevLett.97.094102. PMID 17026366. S2CID 18365246.
- ^ M. E. J. Newman (2003). "Mixing patterns in networks". Physical Review E. 67 (2): 026126. arXiv:cond-mat/0209450. Bibcode:2003PhRvE..67b6126N. doi:10.1103/PhysRevE.67.026126. PMID 12636767. S2CID 15186389.
- ^ Marwan N, Donges JF, Zou Y, Donner RV, Kurths J (2009). "Complex network approach for recurrence analysis of time series". Physics Letters A. 373 (46): 4246–4254. arXiv:0907.3368. Bibcode:2009PhLA..373.4246M. doi:10.1016/j.physleta.2009.09.042. ISSN 0375-9601. S2CID 7761398.
- ^ Donner RV, Heitzig J, Donges JF, Zou Y, Marwan N, Kurths J (2011). "The Geometry of Chaotic Dynamics – A Complex Network Perspective". European Physical Journal B. 84 (4): 653–672. arXiv:1102.1853. Bibcode:2011EPJB...84..653D. doi:10.1140/epjb/e2011-10899-1. ISSN 1434-6036. S2CID 18979395.
- ^ Feldhoff JH, Donner RV, Donges JF, Marwan N, Kurths J (2013). "Geometric signature of complex synchronisation scenarios". Europhysics Letters. 102 (3) 30007. arXiv:1301.0806. Bibcode:2013EL....10230007F. doi:10.1209/0295-5075/102/30007. ISSN 1286-4854. S2CID 119118006.
- ^ Waxman BM (1988). "Routing of multipoint connections". IEEE Journal on Selected Areas in Communications. 6 (9): 1617–1622. doi:10.1109/49.12889.
- ^ Franch, F.; Nocciola, L.; Vouldis, A. (April 2024). "Temporal networks and financial contagion". Journal of Financial Stability. 71 101224. doi:10.1016/j.jfs.2024.101224.
- ^ Li, A.; Zhou, L.; Su, Q.; Cornelius, S.P.; Liu, Y.; L., Wang; Levin, S.A. (8 May 2020). "Evolution of cooperation on temporal networks". Nature Communications. 11 (2259) 2259. arXiv:1609.07569. Bibcode:2020NatCo..11.2259L. doi:10.1038/s41467-020-16088-w. PMID 32385279.
- ^ Jordan, D.G.; Winer, E.S.; Salem, T. (2020). "The current status of temporal network analysis for clinical science: Considerations as the paradigm shifts?". J Clin Psychol. 76 (9): 1591–1612. doi:10.1002/jclp.22957. PMID 32386334.
- ^ Masuda, N.; Holme, P. (2013). "Predicting and controlling infectious disease epidemics using temporal networks". F1000Prime Reports. 5: 6. doi:10.12703/P5-6. PMC 3590785. PMID 23513178.
- ^ Newman M, Barabási AL, Watts DJ, eds. (2006). The Structure and Dynamics of Networks. Princeton, N.J.: Princeton University Press.
- ^ Callaway DS, Newman ME, Strogatz SH, Watts DJ (December 2000). "Network robustness and fragility: percolation on random graphs". Physical Review Letters. 85 (25): 5468–5471. arXiv:cond-mat/0007300. Bibcode:2000PhRvL..85.5468C. doi:10.1103/PhysRevLett.85.5468. PMID 11136023. S2CID 2325768.
Books
[edit]- Dorogovtsev SN, Mendes JR (2003). Evolution of Networks: from biological networks to the Internet and WWW. Oxford University Press. ISBN 978-0-19-851590-6.
- Caldarelli G (2007). Scale-Free Networks. Oxford University Press. ISBN 978-0-19-921151-7.
- Barrat A, Barthelemy M, Vespignani A (2008). Dynamical Processes on Complex Networks. Cambridge University Press. ISBN 978-0-521-87950-7.
- Estrada E (2011). The Structure of Complex Networks: Theory and Applications. Oxford University Press. ISBN 978-0-199-59175-6.
- Soramaki K, Cook S (2016). Network Theory and Financial Risk. Risk Books. ISBN 978-1-78272-219-9.
- Latora V, Nicosia V, Russo G (2017). Complex Networks: Principles, Methods and Applications. Cambridge University Press. ISBN 978-1-107-10318-4.
External links
[edit]- netwiki Archived 2014-12-24 at the Wayback Machine Scientific wiki dedicated to network theory
- New Network Theory Archived 2021-05-05 at the Wayback Machine International Conference on 'New Network Theory'
- Network Workbench Archived 2010-08-26 at the Wayback Machine: A Large-Scale Network Analysis, Modeling and Visualization Toolkit
- Optimization of the Large Network Archived 2021-09-22 at the Wayback Machine doi:10.13140/RG.2.2.20183.06565/6
- Network analysis of computer networks Archived 2014-06-17 at the Wayback Machine
- Network analysis of organizational networks Archived 2021-05-05 at the Wayback Machine
- Network analysis of terrorist networks
- Network analysis of a disease outbreak
- Link Analysis: An Information Science Approach Archived 2018-04-05 at the Wayback Machine (book)
- Connected: The Power of Six Degrees (documentary)
- A short course on complex networks Archived 2021-04-15 at the Wayback Machine
- A course on complex network analysis by Albert-László Barabási
- The Journal of Network Theory in Finance Archived 2019-12-06 at the Wayback Machine
- Network theory in Operations Research Archived 2016-09-15 at the Wayback Machine from the Institute for Operations Research and the Management Sciences (INFORMS)
Network theory
View on GrokipediaHistory and Development
Origins in Graph Theory
Graph theory, the mathematical study of graphs as formal structures comprising vertices connected by edges, originated in the 18th century with foundational work on connectivity and traversal problems.[5] The discipline's inception is commonly traced to Leonhard Euler's 1736 solution to the Seven Bridges of Königsberg problem, which posed whether it was possible to traverse all seven bridges in the Prussian city of Königsberg (now Kaliningrad) exactly once and return to the starting point. Euler modeled the landmasses as vertices and the bridges as edges in a multigraph, proving that no such Eulerian cycle existed because exactly two vertices had odd degree, violating the necessary condition for an Eulerian circuit in a connected graph. This analysis established core concepts of graph traversal, paths, and connectivity, marking the first systematic application of graph-theoretic reasoning to a combinatorial problem.[6] In the 19th and early 20th centuries, graph theory expanded through contributions focused on enumeration and structural properties. Arthur Cayley advanced the field in 1857 by developing methods for enumerating trees, acyclic connected graphs, laying groundwork for counting distinct graph structures and their applications in chemical and combinatorial contexts. Later, Dénes Kőnig extended graph theory in 1931 with his work on matchings in bipartite graphs, proving the equivalence between the size of a maximum matching and a minimum vertex cover, which introduced duality principles pivotal to optimization in graphs.[7][8] By the mid-20th century, graph theory transitioned from abstract mathematics to applied domains, particularly in modeling social structures. Frank Harary's collaborations in the 1950s, notably the 1953 monograph with Robert Z. Norman, demonstrated graph theory's utility as a tool for analyzing social networks, balance in signed graphs, and group dynamics, bridging pure theory with interdisciplinary applications in sociology and psychology. This period saw graphs represented via adjacency matrices to facilitate computational analysis, though detailed formulations emerged later.Key Contributors and Milestones
In the mid-20th century, Anatol Rapoport played a pivotal role in extending graph theory to the analysis of social structures, particularly during the 1940s and 1950s. Rapoport's work focused on modeling information diffusion and connectivity in populations, introducing concepts like biased nets to account for socio-structural preferences in interactions, which laid foundational ideas for probabilistic approaches in social network studies.[9][10] Sociologist Jacob L. Moreno also contributed significantly in the 1930s through sociometry, developing sociograms—graph representations of social relationships—to study group dynamics and interpersonal connections, establishing early empirical methods in social network analysis.[10] A major milestone came in 1959–1960 with the introduction of random graph models by Paul Erdős and Alfréd Rényi, which shifted network theory toward probabilistic methods by examining the evolution and properties of graphs generated randomly. Their seminal papers demonstrated thresholds for connectivity and component formation, providing mathematical tools to study large-scale networks beyond deterministic structures.[11][12] Stanley Milgram's 1967 small-world experiment further advanced the field by empirically investigating path lengths in social networks, revealing that individuals in the United States were typically connected through an average of six intermediaries, thus popularizing the "six degrees of separation" concept and inspiring subsequent research on network diameter.[13] In 1999, Albert-László Barabási and Réka Albert developed the theory of scale-free networks, proposing that many real-world networks exhibit power-law degree distributions arising from growth and preferential attachment mechanisms, where new nodes preferentially connect to highly connected ones. This model explained heterogeneous connectivity patterns observed in systems like the World Wide Web and biological networks.[14] Key organizational milestones included the formation of the International Network for Social Network Analysis (INSNA) in 1977 by Barry Wellman, which fostered interdisciplinary collaboration and standardized methodologies in the field.[15] Additionally, the 1990s saw the rise of computational tools such as Pajek, developed by Vladimir Batagelj and Andrej Mrvar, enabling efficient analysis and visualization of large networks with millions of vertices.[16]Fundamental Concepts
Graphs and Networks
In graph theory, a graph is formally defined as an ordered triple $ G = (V(G), E(G), \psi_G) $, where $ V(G) $ is a nonempty finite set of vertices, $ E(G) $ is a set of edges disjoint from $ V(G) $, and $ \psi_G $ is an incidence function that associates each edge with an unordered pair of vertices (the ends of the edge).[17] This structure models pairwise relations between objects, with vertices representing entities and edges representing connections.[18] Graphs can be undirected, where edges have no direction, or directed, where edges are ordered pairs indicating orientation.[17] Networks extend this framework by applying graphs to real-world systems, often as labeled or weighted versions where vertices and edges carry attributes such as identities, capacities, or strengths to capture relational structures like social ties or physical interactions, rather than focusing solely on abstract combinatorial properties.[19] In this context, networks emphasize the modeling of complex systems in fields like sociology and physics, distinguishing them from pure mathematical graphs.[20] Key terminology includes simple graphs, which contain no loops (edges connecting a vertex to itself) or multiple edges between the same pair of vertices, and multigraphs, which permit multiple edges between vertices but typically exclude loops.[18] Two graphs are isomorphic if there exists a bijection between their vertex sets that preserves adjacency, meaning they share identical structural properties despite different labelings.[21] A graph is connected if there is a path—a sequence of adjacent edges—between every pair of distinct vertices.[21] The concept of networks gained prominence in the mid-20th century, particularly in sociology through structural balance theory, which used graphs to analyze interpersonal relations and group dynamics. In physics, random graph models introduced around the same period further popularized networks for studying emergent properties in large-scale systems.[11] This shift marked a departure from classical graph theory's combinatorial focus toward interdisciplinary applications in relational data.[19]Nodes, Edges, and Basic Properties
In network theory, nodes, also referred to as vertices, serve as the basic building blocks representing discrete entities within a system, such as individuals in social networks or proteins in biological interaction networks.[22][23] These nodes encapsulate the primary objects of study and can carry attributes, such as labels identifying categories or states describing dynamic properties like activation levels.[24] For instance, in a social network, a node's label might denote gender, while in a neural network, its state could indicate firing activity.[25] Edges, alternatively called links, represent the connections or interactions between nodes, forming the structure that defines relational dependencies in the network.[26] Edges can be undirected, implying a symmetric relationship where traversal is possible in either direction, or directed, indicating an asymmetric interaction such as influence from one node to another in communication networks.[27] Additionally, edges may be unweighted, signifying only the existence of a tie without quantitative measure, or weighted, incorporating a numerical value to reflect the intensity, capacity, or frequency of the connection, as seen in transportation networks where weights denote travel times.[27] Certain network representations permit self-loops, edges that connect a node to itself to model reflexive processes like self-regulation in biological systems, and multiple edges between the same pair of nodes, allowing for multigraphs that capture parallel or repeated interactions.[27] For example, directed graphs, a common network type, emphasize the orientation of edges to model flows or hierarchies.[28] Basic properties of nodes and edges provide essential metrics for understanding local network structure. The degree of a node is defined as the total number of edges directly connected to it, serving as a primary indicator of a node's connectivity and influence within its immediate neighborhood.[29] In undirected networks, this count is straightforward, while in directed networks, it splits into in-degree (incoming edges) and out-degree (outgoing edges).[30] The clustering coefficient quantifies the local density of triangles around a node, calculated as the ratio of the number of actual triangles involving the node to the maximum possible triangles among its neighbors, thereby measuring the extent to which connected nodes tend to form closed triads.[31] Introduced by Watts and Strogatz, this property highlights tendencies toward local cohesion, with values ranging from 0 (no triangles) to 1 (fully connected neighborhood).[31] Path length refers to the shortest distance between two nodes, defined as the minimum number of edges required to traverse from one to the other along any connecting path.[32] This measure captures the efficiency of local reachability, distinguishing direct connections (length 1) from longer chains.[33] A key aggregate property is the average degree , which for undirected networks is computed as , where denotes the total number of edges and the number of nodes; this formula reveals the overall connectivity density and is particularly useful for identifying sparse networks where remains far below the maximum possible value of .[34] Such sparsity is common in real-world networks, emphasizing efficient structures over dense ones.[34]Network Types
Network theory encompasses a variety of network architectures that differ in the directionality, weighting, and structural organization of edges connecting nodes. These distinctions allow for modeling diverse relational systems, from symmetric social ties to asymmetric information flows. Undirected networks represent relations where connections are reciprocal, such as friendships in social groups, where the presence of an edge between two nodes implies mutual linkage without specified direction. In these networks, the adjacency matrix is symmetric, meaning that if node i is connected to node j, then node j is connected to node i, reflecting the bidirectional nature of the relation.[35][36] Directed networks, also known as digraphs, model asymmetric relations where edges have a specific orientation, such as citations in academic literature, where one paper references another but not vice versa. Here, each node has an in-degree, counting incoming edges, and an out-degree, counting outgoing edges, enabling analysis of influence flows or dependencies that undirected models cannot capture. This structure is essential for systems like communication networks or web links, where directionality conveys causality or hierarchy.[37][38] Weighted networks extend both undirected and directed forms by assigning numerical values to edges, representing the strength or intensity of connections, such as traffic volumes on transportation routes. These weights can quantify varying interaction levels, with higher values indicating stronger ties, and are often normalized— for instance, by dividing edge weights by the sum of weights incident to a node—to facilitate comparisons or probabilistic interpretations in analyses like random walks. Normalization methods, such as row normalization in adjacency matrices, ensure weights sum to unity per node, aiding in the computation of metrics like weighted degrees or strengths.[39] Beyond these core types, several specialized architectures address complex relational structures. Bipartite networks consist of two disjoint node sets, with edges connecting only between sets, such as collaborations between authors and publications, precluding intra-set connections and enabling projections onto unipartite graphs for further analysis. Multilayer networks incorporate multiple edge types or layers, each representing distinct interaction modes—like social and professional ties—allowing nodes to participate across layers with interlayer dependencies. Signed networks include positive and negative edges to model affinity or antagonism, as in trust-distrust relations, where balance theory posits structural stability when positive edges form clusters and negative edges span them.[40][41][42]Mathematical Foundations
Matrix Representations
In network theory, matrix representations provide linear algebraic encodings of graph structures, enabling efficient computation and analysis of connectivity and paths. The adjacency matrix $ A $ of a graph with $ n $ vertices is an $ n \times n $ square matrix where the entry $ A_{ij} = 1 $ if there is an edge from vertex $ i $ to vertex $ j $, and $ A_{ij} = 0 $ otherwise.[43] For undirected networks, where edges lack direction, the adjacency matrix is symmetric, satisfying $ A = A^T $, because an edge between $ i $ and $ j $ implies the same for $ j $ and $ i $.[43] In directed networks, the matrix is generally asymmetric, reflecting the orientation of edges.[43] The incidence matrix $ B $ offers an alternative encoding, with rows corresponding to the $ n $ vertices and columns to the $ m $ edges. Each entry $ B_{ve} = 1 $ if vertex $ v $ is incident to edge $ e $, and 0 otherwise, capturing vertex-edge incidences without orientation.[44] This unoriented form is particularly useful in flow problems, such as modeling commodity flows across edges while respecting vertex capacities.[44] A key property is that the product $ B B^T $ yields a matrix whose diagonal entries are the degrees of the vertices (forming the degree matrix $ D $) and off-diagonal entries indicate shared incidences, resulting in $ B B^T = D + A $ for simple undirected graphs without multiple edges.[45] The Laplacian matrix $ L $, defined as $ L = D - A $, combines the degree matrix $ D $ (a diagonal matrix with vertex degrees on the diagonal) and the adjacency matrix to encode diffusion-like processes on the network.[46] The eigenvalues of $ L $ provide insights into network connectivity; specifically, the second smallest eigenvalue, known as the algebraic connectivity or Fiedler value, quantifies the graph's robustness to disconnection, with higher values indicating better overall connectivity.[47] A graph is connected if and only if this eigenvalue is positive.[47] Powers of the adjacency matrix reveal path structures: the entry $ (A^k)_{ij} $ counts the number of walks of length $ k $ from vertex $ i $ to vertex $ j $, derived from the matrix multiplication rule where each step corresponds to an edge traversal.[43] This property stems from the fact that multiplying $ A $ by itself accumulates adjacency relations over multiple steps, enabling the enumeration of closed walks (when $ i = j $) or open paths in acyclic cases.[43]Degree Distributions and Motifs
In network theory, the degree distribution $ P(k) $ represents the probability that a randomly selected node has degree $ k $, where degree denotes the number of edges connected to the node.[48] This distribution provides a fundamental statistical description of connectivity patterns, capturing how connections are unevenly spread across nodes. Empirically, $ P(k) $ is fitted by constructing histograms from the degree sequence of all nodes in the observed network, allowing researchers to identify underlying forms such as exponential or power-law tails.[49] In scale-free networks, like those modeling the internet or protein interactions, $ P(k) $ follows a power-law $ P(k) \sim k^{-\gamma} $ with $ 2 < \gamma < 3 $, resulting in a few highly connected hub nodes that dominate the network's structure and influence its robustness to failures. Network motifs extend this analysis to local substructures, defined as small induced subgraphs of 3 to 5 nodes that recur at frequencies significantly higher than in randomized null models. These patterns, such as triads or directed loops, reveal building blocks of network architecture that may underpin functional properties. Detection involves subgraph enumeration algorithms that systematically identify all possible small subgraphs and count their occurrences; a widely used tool is mfinder, which employs edge-coloring techniques for efficient sampling in large networks.[50] Significance is tested by generating an ensemble of randomized networks—typically preserving the original degree distribution and edge density—and computing z-scores or p-values for motif frequencies, ensuring deviations are not due to global constraints. Hub nodes from power-law degree distributions exemplify how local connectivity statistics enable global phenomena, such as efficient information flow in transportation networks. In biological systems, the feed-forward loop (FFL) motif—a triad where one node regulates both a second node and a target, with the second also regulating the target—appears enriched in gene regulatory networks.[51] Coherent FFLs, with consistent regulatory signs, promote signal coherence by accelerating responses to persistent inputs while delaying transient ones, thus filtering noise and enhancing decision-making in processes like bacterial chemotaxis.[51]Characteristic Network Models
Characteristic network models provide foundational frameworks for understanding the structural properties of networks by generating synthetic graphs that mimic observed empirical features. These models emphasize generative processes that produce specific degree distributions and topological characteristics, enabling theoretical analysis of network behavior. The Erdős–Rényi model, denoted as G(n, p), constructs a random graph with n nodes where each possible edge is included independently with probability p. In this model, the degree of a node follows a binomial distribution Bin(n-1, p), leading to a relatively uniform degree distribution across nodes. A key property is the phase transition at the percolation threshold p = 1/n, where a giant connected component emerges, marking the shift from fragmented to cohesive network structure.[12] The small-world network model, introduced by Watts and Strogatz, starts with a regular lattice and rewires a fraction of edges randomly to create intermediate structures between order and randomness. This rewiring preserves high clustering coefficients typical of lattices while drastically reducing average path lengths, resulting in networks that are both locally dense and globally efficient. The model's small-world regime is quantified by the clustering ratio (close to 1 for high clustering) and the path length ratio (close to 1 for short paths), where and denote clustering coefficient and average path length, respectively, compared to random graph equivalents.[52] Scale-free networks, as proposed by Barabási and Albert, emerge through a generative process involving continuous growth (adding new nodes over time) and preferential attachment (new nodes connect to existing nodes with probability proportional to their degree). This mechanism yields a power-law degree distribution , where typically ranges from 2 to 3, characterized by a few highly connected hubs and many low-degree nodes, capturing the heterogeneity observed in many real-world systems.[53] In comparison, the Erdős–Rényi model emphasizes uniformity with homogeneous degrees and sharp transitions, suitable for studying baseline random connectivity; the small-world model balances local clustering with global reach for efficient information propagation; and scale-free models highlight heterogeneity and robustness through hubs, each addressing distinct empirical network motifs without overlapping generative assumptions.[12][52][53]Static Network Analysis
Centrality Measures
Centrality measures in network theory quantify the importance or influence of nodes based on their structural positions within a graph. These metrics help identify key actors in social, biological, or technological networks by evaluating factors such as connectivity, proximity, and mediation roles. Developed primarily in the context of social network analysis, centrality measures provide insights into how nodes facilitate information flow, resource distribution, or control in a system. Degree centrality is the simplest measure, defined as the normalized number of direct connections a node has to others in the network. For a node in a graph with nodes, it is given by , where is the degree of . This metric assumes that a node's influence is proportional to its immediate connections, making it computationally efficient for large networks but limited in capturing indirect influences. Betweenness centrality assesses a node's role as an intermediary on shortest paths between other nodes, highlighting its potential to control communication or flow. It is formalized as , where is the total number of shortest paths from node to , and is the number of those paths passing through . The naive computation requires evaluating all pairs of nodes, leading to time complexity, but Brandes' algorithm improves this to for sparse graphs with edges by using breadth-first search and dependency accumulation.[54] Closeness centrality evaluates a node's efficiency in reaching all others, based on its average distance to the rest of the network. It is defined as , where is the shortest-path distance between and . This measure, originally motivated by communication efficiency in group tasks, favors nodes that minimize the total path length to others, though it assumes a connected graph and can be sensitive to disconnected components.[55] Eigenvector centrality extends degree centrality by accounting for the centrality of a node's neighbors, positing that connections to influential nodes enhance a node's own importance. It satisfies the equation , where is the adjacency matrix and is the largest eigenvalue; the solution is the principal eigenvector of . This recursive definition, solved via power iteration, captures global network structure but requires the graph to be strongly connected for convergence. A damped variant, PageRank, incorporates a teleportation probability to address issues like dangling nodes and sinks, defined as , where is the damping factor (typically 0.85) and is the number of nodes; it was pivotal in web search ranking.[56][57] Despite their utility, centrality measures exhibit limitations, particularly in scalability for large networks where exact computation becomes prohibitive due to high time complexity. For instance, betweenness and closeness require all-pairs shortest paths, which is infeasible for graphs with millions of nodes, prompting approximations via sampling or heuristics that trade accuracy for speed. These measures are also sensitive to network size and density, potentially overemphasizing local structure in sparse graphs.[58][59]Assortative Mixing Patterns
Assortative mixing patterns in networks refer to the tendency for nodes to connect preferentially to others with similar or dissimilar attributes, most commonly analyzed through node degrees. This phenomenon influences network structure and dynamics, particularly how high-degree nodes (hubs) link to one another. In assortative mixing, hubs connect to other hubs, promoting clustering among similar nodes, while in disassortative mixing, hubs link to low-degree nodes, creating a more hierarchical structure. These patterns are quantified using the assortativity coefficient, which measures the correlation in degrees at the ends of edges.[60] The assortativity coefficient $ r $ is defined as the Pearson correlation coefficient of the degrees of nodes connected by edges:Community Detection
Community detection in network theory involves identifying groups of nodes that are more densely connected internally than to the rest of the network, revealing modular structures that often correspond to functional units in real-world systems. These communities can enhance understanding of network organization, such as social circles in friendship networks or protein complexes in biological networks. Methods for community detection typically aim to partition the graph into subgraphs that maximize intra-community ties while minimizing inter-community connections, addressing the challenge of scalability in large, sparse networks. One prominent approach is modularity optimization, which quantifies the strength of community divisions by comparing the observed density of edges within communities to what would be expected in a random network with the same degree sequence. The modularity $ Q $ is defined asApplications in Social Systems
Social Network Analysis
Social network analysis (SNA) applies network theory to examine the structure and dynamics of human relationships, modeling social systems as graphs where nodes represent actors such as individuals or groups, and edges denote ties like friendships, collaborations, or communications. This approach emphasizes how positions— the specific locations of actors within the network— and roles— the recurring patterns of ties actors exhibit— influence behavior, information flow, and social influence. By quantifying relational patterns, SNA reveals underlying social mechanisms beyond individual attributes, such as how ties facilitate resource access or constrain opportunities.[67] A fundamental distinction in SNA lies between ego networks and whole networks. Ego networks center on a focal actor (the ego) and their direct connections (alters), capturing local structures like support circles or personal influence spheres without requiring data on the broader population; this method is efficient for large-scale surveys but limits insights into global patterns. In contrast, whole networks encompass all actors and ties within a bounded population, such as a workplace or community, enabling analysis of collective properties like cohesion or fragmentation, though data collection is more resource-intensive.[67][68] Key metrics in SNA include density and reciprocity, which assess network cohesion. Density is the ratio of observed ties to the maximum possible ties, reflecting how interconnected a social group is; low density may indicate sparse relations conducive to innovation spread, while high density suggests tight-knit communities with redundant information. Reciprocity measures the mutuality of directed ties, calculated as the proportion of dyads where both actors connect to each other, often signaling trust or balanced exchanges in relationships like alliances or conversations. Another pivotal metric is structural holes, gaps between non-adjacent actors that create brokerage advantages; actors spanning these holes gain control over information flows and novel opportunities, as theorized by Burt (1992).[67][69][70] To model tie formation statistically, building on the exponential family of probability distributions for directed graphs introduced by Holland and Leinhardt (1981)[71], Frank and Strauss (1986) developed Markov random graph models, providing a framework for exponential random graph models (ERGMs) that treat observed networks as realizations from a probability distribution conditioned on network statistics like triad closures or degree distributions. ERGMs estimate parameters that explain why ties exist, accounting for dependencies such as homophily or transitivity, and are widely used to test hypotheses about social processes in empirical data.[72] SNA has illuminated processes like the diffusion of innovations, where Granovetter's (1973) strength of weak ties argument demonstrates that loose acquaintances bridge dense clusters, accelerating the spread of ideas or behaviors across diverse groups more effectively than strong ties within them. In online social networks, such as Facebook, analyses reveal similar patterns: users form dense ego networks of close friends but rely on weak ties for broader reach, with community detection uncovering hierarchical structures of overlapping groups that influence content virality and user engagement. Centrality measures in these contexts identify key influencers, as detailed in broader static analysis sections.[73][74]Link Analysis
Link analysis encompasses computational techniques that derive insights from the structure and semantics of links in relational data, particularly in directed graphs representing hyperlinks, citations, or transactions. These methods leverage the topology of connections to infer importance, relevance, or irregularities, with foundational applications in web search and information retrieval. By modeling networks where nodes represent entities like web pages or documents and edges denote relationships such as incoming links, link analysis quantifies authority and influence through iterative scoring mechanisms. The Hyperlink-Induced Topic Search (HITS) algorithm, introduced by Jon Kleinberg, identifies hubs and authorities within a web graph by assigning scores based on mutual reinforcement. In this approach, a hub score measures a page's value in pointing to high-quality authorities, while an authority score reflects the quality of pages linking to it; these scores are computed iteratively using adjacency matrices until convergence, treating the problem as finding principal eigenvectors of the hub-authority product matrix. HITS operates on a focused subgraph derived from a query, expanding to nearby pages to mitigate noise from the broader web. This method has been influential in topic-specific ranking, though it is susceptible to spam through link farms. PageRank, developed by Sergey Brin and Larry Page, provides a global measure of page importance by simulating a random surfer model on the web graph. The score for node is given byApplications in Physical and Biological Systems
Electrical Network Analysis
Electrical network analysis applies graph-theoretic principles from network theory to model and solve problems in electrical circuits and systems, treating components like resistors, capacitors, and inductors as edges connecting nodes (junctions). This approach enables the representation of complex circuits as graphs, where vertices correspond to nodes and edges to circuit elements, facilitating the use of linear algebra and combinatorial optimization for analysis. By framing electrical flows as processes on networks, engineers can predict behaviors such as current distribution, voltage drops, and signal propagation, which is essential for designing reliable power systems and integrated circuits. Kirchhoff's laws serve as fundamental network constraints in this framework, expressed through the graph's incidence matrix. The incidence matrix $ \mathbf{A} $ of a directed graph with $ n $ nodes and $ m $ edges is an $ n \times m $ matrix where each column corresponds to an edge, with entries $ +1 $ at the row of the "from" node, $ -1 $ at the "to" node, and 0 elsewhere; this matrix encodes the topology for applying Kirchhoff's current law (KCL) and voltage law (KVL). KCL states that the algebraic sum of currents entering a node is zero, which translates to $ \mathbf{A} \mathbf{i} = 0 $ for current vector $ \mathbf{i} $, ensuring conservation of charge across the network. Similarly, KVL asserts that the algebraic sum of voltages around any closed loop is zero, represented as $ \mathbf{B} \mathbf{v} = 0 $, where $ \mathbf{B} $ is the loop matrix derived from the incidence matrix's null space, and $ \mathbf{v} $ is the voltage vector across edges. These matrix formulations allow systematic enforcement of physical laws in large-scale circuit simulations. Impedance and admittance matrices provide algebraic tools for solving linear electrical networks under steady-state conditions. The admittance matrix, or Y-matrix, relates node voltages to injected currents via $ \mathbf{i} = \mathbf{Y} \mathbf{v} $, where diagonal elements represent the sum of admittances connected to a node, and off-diagonals are negative sums of admittances between nodes. In power systems, the Y-bus matrix is a specialized form of the admittance matrix, constructed from line impedances and shunt elements to model bus interconnections in transmission grids. To solve for unknown voltages or currents, Gaussian elimination is applied to the Y-matrix equations, reducing the system to triangular form for efficient back-substitution, particularly useful in sparse networks where only a few non-zero entries exist due to localized connections. This method scales well for large power networks, enabling load flow analysis without explicit loop identification. Graph-theoretic tools extend these analyses by optimizing circuit layouts and performance. Minimum spanning trees (MSTs) are used for wiring optimization in electrical networks, selecting a subset of edges that connects all nodes with minimal total impedance or cost, as in printed circuit board routing where Kruskal's or Prim's algorithms minimize wire length while avoiding cycles. Shortest paths algorithms, such as Dijkstra's, model signal delay by treating edge weights as propagation times or resistances, identifying the minimal-delay route between components in integrated circuits. These combinatorial approaches integrate seamlessly with electrical constraints, enhancing design efficiency in high-density layouts. In VLSI design, network theory aids in managing interconnect delays and power distribution across millions of transistors modeled as graphs, where centrality measures help prioritize critical paths to reduce latency. For power grid stability, spectral graph theory analyzes eigenvalue distributions of the Laplacian matrix (derived from the incidence matrix) to assess vulnerability to cascading failures, as demonstrated in models of blackout propagation. Additionally, Fourier analysis on graphs extends classical signal processing to irregular electrical networks, decomposing voltages or currents into eigenbasis of the graph Laplacian for frequency-domain responses, useful in filtering noise in sensor networks or harmonic analysis in AC circuits.Biological Network Analysis
Biological network analysis applies graph theory to model and interpret interactions within living systems, ranging from molecular to ecological scales. These networks capture the interconnected nature of biological processes, revealing emergent properties such as robustness and modularity that underpin cellular function and organismal adaptation. Key types include protein-protein interaction (PPI) networks, metabolic networks, and neural networks, each exhibiting distinct topological features that reflect evolutionary pressures and functional constraints.[79] PPI networks represent physical or functional associations between proteins, often displaying scale-free degree distributions where a few highly connected hubs interact with many partners. This topology arises from evolutionary mechanisms like gene duplication followed by divergence, where duplicated genes retain some interactions while accumulating new ones, leading to power-law distributions observed across species from yeast to humans.[79] Metabolic networks map enzymatic reactions converting substrates to products, typically showing bow-tie structures with broad input and output funnels for efficient resource utilization. Neural networks, or connectomes, depict synaptic connections between neurons, characterized by small-world properties that balance local clustering and global efficiency for rapid information processing.[80][81] Analysis of these networks highlights robustness to random failures, attributed to heterogeneous degree distributions where most nodes have low connectivity, allowing the system to tolerate perturbations without collapse. In PPI networks, highly connected hub proteins are often essential, as their removal leads to lethality, underscoring the correlation between centrality and functional importance. Synthetic lethality emerges in gene regulatory networks when pairwise gene disruptions cause cell death despite individual viability, often due to redundant pathways; this phenomenon is exploited in cancer therapies targeting vulnerabilities in mutated cells. Scale-free motifs, such as recurrent subgraphs, further contribute to evolutionary stability by facilitating adaptive rewiring.[82][83] Methods for analyzing biological networks include flux balance analysis (FBA) for metabolic pathways, which optimizes steady-state fluxes under stoichiometric constraints to predict growth rates and metabolite flows without kinetic details. For gene regulation dynamics, Boolean networks model gene states as binary (on/off) with logical rules, simulating attractor states that represent stable phenotypes like cell differentiation. These approaches reveal how network topology influences dynamical behaviors, such as oscillatory patterns in regulatory circuits.[80][84] Examples abound in ecological and neural contexts. Food webs, modeling predator-prey interactions, often exhibit disassortative mixing by degree, where high-degree species (e.g., basal producers) preferentially connect to low-degree species, which can enhance stability against species loss.[85] Brain connectomes, such as those from the human or Drosophila, demonstrate modular organization with rich-club hubs integrating sensory-motor functions.[81] Evolutionary models like duplication-divergence simulate PPI network growth, reproducing observed scale-free properties and predicting interaction retention probabilities around 0.3–0.4 for realism.[86]Dynamic and Spatiotemporal Networks
Temporal Networks
Temporal networks, also known as time-varying or dynamic networks, represent systems where the presence or absence of connections between nodes evolves over time, contrasting with static networks that assume fixed topologies. These networks are formalized through representations such as time-stamped contact sequences, denoted as triples indicating an edge between nodes and at time , or as discrete snapshots of the adjacency matrix at successive intervals. This temporal structure captures real-world phenomena like human interactions or transportation flows, where links are intermittent rather than persistent. A key distinction from static networks lies in the concept of temporal paths, or time-respecting walks, which require that the sequence of edge timestamps is non-decreasing () to ensure causality in information or influence propagation. Unlike shortest paths in static graphs, temporal paths prioritize arrival time over mere hop count, often computed via efficient algorithms that aggregate over time windows to assess reachability. This framework highlights how temporal ordering can dramatically alter network efficiency; for instance, in empirical datasets like mobile phone calls, the fraction of reachable node pairs via time-respecting paths can be orders of magnitude lower than in the static projection. Metrics for temporal networks extend static centrality measures to account for time. Temporal betweenness centrality quantifies a node's role in facilitating time-respecting paths between all pairs, defined as , where is the number of time-respecting paths from to , and passes through . This metric, applied to datasets such as email communications, reveals time-dependent bottlenecks not visible in aggregated graphs. Another important property is burstiness, characterizing the irregular timing of contacts through the inter-event time distribution, often following a power-law with , leading to a burstiness coefficient where and are the standard deviation and mean of inter-event times. In contact sequences from proximity sensors, high burstiness () indicates clustered interactions, slowing diffusion compared to Poissonian processes. Models of temporal networks aim to replicate these empirical features. Time-respecting walks form the basis for analyzing dynamical processes, enforcing chronological order in path traversal, which is essential for simulating realistic spreading without hindsight. A prominent generative model is the activity-driven network, where each node has an intrinsic activity potential drawn from a distribution (e.g., power-law), generating outgoing edges to randomly selected nodes at each discrete time step , with edges decaying after a persistence time.[87] This approach naturally produces bursty degree sequences and heterogeneous connectivity without preferential attachment, matching observations in online messaging data where active users drive transient hubs.[87] Applications of temporal networks are prominent in modeling epidemic spread on dynamic contacts. In susceptible-infected (SI) models over time-varying graphs, burstiness and temporal correlations increase outbreak thresholds; for example, simulations on empirical face-to-face interaction data show that ignoring timing overestimates spread by up to 50%. Activity-driven models further reveal that the epidemic threshold for SIS processes is , where and are infection and recovery rates, emphasizing the role of activity heterogeneity in containment strategies.[87] For evolving social ties, temporal representations track tie reinforcement over repeated contacts, as in weighted temporal graphs where edge weights accumulate based on interaction frequency, applied to collaboration networks to predict community evolution and influence diffusion.Spatial Networks
Spatial networks are graphs where nodes are embedded in a physical space, such as Euclidean geometry, and the formation of edges is influenced by the spatial positions of the nodes. In these networks, the probability of an edge between two nodes typically decreases with their Euclidean distance, reflecting constraints like cost or physical feasibility. For instance, connection probabilities often follow a power-law decay, , where is the Euclidean distance and for long-range links in systems like airline routes exceeding 100 km.[88] This embedding affects network topology, promoting local connections and limiting long-range ones unless mediated by hubs.[89] A prominent class of spatial networks is planar graphs, which can be drawn on a plane without edge crossings, a property essential for systems like road layouts or power grids. Planar graphs satisfy Euler's formula, , where is the number of nodes, the edges, and the faces, implying an upper bound for simple connected graphs.[88] Spatial constraints in these networks enforce low average degrees, typically around 3 in European road systems or 2 in U.S. ones, with degree distributions that are exponentially decaying rather than power-law.[88] Crossings are minimized to optimize efficiency, as seen in urban street patterns that balance connectivity and space.[90] Key metrics in spatial networks capture geometric influences on structure. Spatial clustering coefficients are elevated due to proximity-based connections, with average values around 0.59 in geometric random graphs and higher in transportation systems compared to non-spatial counterparts.[88] Distance decay manifests as a reduction in connection probability or link strength with increasing separation, often exponentially in short-range systems (e.g., scale ~1000 km in airlines) or via power laws like for urban trips over 1–100 km.[88] These metrics highlight how space induces assortativity by distance, where nearby nodes form denser subgraphs.[89] Models of spatial networks include lattice structures, which are regular grids enforcing planarity and short path lengths scaling as in two dimensions.[88] Navigation graphs, such as road networks, exhibit betweenness centrality hotspots at key junctions, enabling efficient routing despite spatial embedding; these often combine small-world properties with scale-free hubs for optimal navigability.[88] In applications like transportation, airline networks use gravity models to weight links, where flow with , predicting higher traffic between populous origins and destinations despite distance deterrence.[88] Wireless sensor networks leverage spatial models for coverage, with short-range links modeled via distance-dependent probabilities to ensure connectivity in ad-hoc deployments.[91] These frameworks underscore spatial networks' role in optimizing real-world systems under geometric constraints.[89]Recurrence Networks
Recurrence networks represent a method for reconstructing complex networks from univariate time series data, enabling the analysis of underlying dynamical systems by mapping temporal recurrences into graph structures.[92] These networks are constructed by interpreting the recurrence matrix of a time series—derived from phase space reconstruction—as the adjacency matrix of a graph, where nodes correspond to states in the embedded phase space and edges indicate proximity between those states. This approach draws from the theory of recurrence plots, originally introduced for visualizing periodicities and structural patterns in dynamical systems. Unlike traditional network representations, recurrence networks emphasize nonlinear dependencies and topological features that reveal the system's complexity without assuming predefined connectivity. The construction of recurrence networks typically begins with phase space reconstruction using time-delay embedding, where a scalar time series $ x(t) $ is transformed into a higher-dimensional vector $ \mathbf{x}(i) = (x(i), x(i+\tau), \dots, x(i+(m-1)\tau)) $, with embedding dimension $ m $ and delay $ \tau $. Edges are then formed based on a distance threshold $ \epsilon $, connecting states $ \mathbf{x}(i) $ and $ \mathbf{x}(j) $ if $ |\mathbf{x}(i) - \mathbf{x}(j)| < \epsilon $, resulting in an $ \epsilon $-recurrence network.[92] Alternative constructions include visibility graphs, which connect time series points if no intermediate point obstructs the "line of sight," effectively capturing monotonic trends, or k-nearest neighbor networks in phase space, where each state links to its $ k $ closest neighbors to form a sparse graph. These methods allow for the inference of causality in multivariate settings through directed links in inter-system recurrence networks, where asymmetric recurrences between paired time series indicate directional influences. Recurrence quantification analysis (RQA) metrics, such as determinism—which measures the fraction of recurrent points forming diagonal lines in the recurrence plot—provide quantitative insights into network properties like periodicity and chaos.[92] In applications, recurrence networks have been employed to analyze climate data, such as palaeoclimate proxy records, where they detect regime transitions and nonlinear dynamics in long-term environmental time series. In neuroscience, these networks reconstruct brain connectivity from electroencephalogram (EEG) signals, revealing functional interactions and detecting nonlinearity in neural activity patterns during cognitive tasks. For instance, RQA metrics applied to EEG-derived recurrence networks quantify determinism to distinguish healthy brain states from pathological ones, such as in epilepsy. Limitations of recurrence networks include sensitivity to the choice of embedding parameters $ m $ and $ \tau $, which must satisfy conditions outlined in Takens' embedding theorem to faithfully reconstruct the attractor from a single time series. Improper selection can lead to distorted topologies, and while the method excels at detecting nonlinearity, it may not reliably differentiate deterministic chaos from stochastic processes without additional validation.Processes on Networks
Spread and Diffusion
The spread and diffusion of information, diseases, or other influences through networks is modeled using dynamical processes that capture propagation along edges. These models reveal how network structure governs the extent and speed of dissemination, often leading to phase transitions where small perturbations grow into large-scale outbreaks. Key frameworks include compartmental models like SIR, percolation approaches for connectivity thresholds, and cascade models for probabilistic activation, each highlighting the role of topology in facilitating or hindering diffusion. The Susceptible-Infected-Recovered (SIR) model partitions network nodes into three states: susceptible (S), capable of infection; infected (I), actively spreading the influence; and recovered (R), immune and non-infectious.[93] Transition from S to I occurs at rate proportional to the number of infected neighbors, while I to R happens at constant rate , independent of contacts.[93] In the mean-field approximation for homogeneous networks, the basic reproduction number , representing the expected secondary infections per case in a fully susceptible population, is , where is the average degree; epidemics occur when .[93] This dynamic yields a sigmoidal growth curve for infections, with the final outbreak size determined by solving self-consistent equations for the probability that a node remains uninfected.[93] Percolation theory analogizes diffusion to the random occupation of network elements, identifying thresholds for the emergence of a giant connected component that enables widespread propagation. In bond percolation, edges are occupied with probability , and the process percolates—forming a spanning cluster—above a critical threshold , beyond which a macroscopic fraction of nodes connects in the giant component. Site percolation similarly occupies nodes with probability , with its threshold marking the onset of a giant susceptible cluster; for Erdős-Rényi networks, and , but these vary with topology. The emergence of the giant component signals a percolation transition, often continuous, where local connections coalesce into global connectivity, mirroring epidemic invasion or information floods. Diffusion processes like the independent cascade model treat spread as a one-shot probabilistic activation along edges, suitable for viral marketing or rumor propagation.[94] Here, each newly activated node attempts to activate each inactive neighbor with success probability (often uniform ), but only once; activations proceed in discrete steps until no further spread occurs.[94] This non-Markovian process captures irreversible influences, with the total activated set depending on initial seeds.[94] Influence maximization, selecting seeds to optimize expected spread, is NP-hard but approximated greedily by iteratively adding the node maximizing marginal gain, achieving a -approximation guarantee.[94] Network heterogeneity profoundly affects diffusion thresholds, particularly in scale-free topologies with power-law degree distributions. High-degree hubs lower the effective percolation threshold, enabling outbreaks at transmission rates near zero in the infinite-size limit, as the branching factor diverges. In such networks, even weak influences can rapidly traverse the system via hubs, contrasting with homogeneous networks requiring for persistence; degree distributions thus modulate vulnerability, with scale-free structures exhibiting vanishing epidemic thresholds.Immunization Strategies
Immunization strategies in network theory aim to mitigate the spread of epidemics or cascading failures by selectively removing or vaccinating nodes, thereby disrupting percolation paths and raising the epidemic threshold. These approaches are particularly crucial in heterogeneous networks, where random immunization often proves inefficient due to the persistence of highly connected hubs. By targeting structurally important nodes, immunization can achieve global protection with a fraction of the resources required for uniform strategies, as demonstrated in models like the susceptible-infected-recovered (SIR) framework. Targeted immunization focuses on vaccinating nodes with high centrality measures, such as degree or betweenness, to maximize disruption of transmission pathways. In high-degree targeted strategies, the most connected nodes (hubs) are prioritized, as their removal fragments the network more effectively than random selection; for instance, in scale-free networks generated by the Barabási-Albert model, immunizing just 16% of the highest-degree nodes can eradicate epidemics, compared to near-total coverage needed for random immunization.[95] Betweenness-based targeting immunizes nodes that lie on many shortest paths, bridging communities and facilitating spread; this approach outperforms degree-based methods in some empirical networks by requiring 5% to 50% fewer vaccinations to achieve the same protection level, though it demands greater computational resources for centrality computation. Overall, targeted strategies are far more efficient than random immunization in heterogeneous topologies but require complete network knowledge, limiting their practicality in real-time scenarios.[95] Acquaintance immunization offers a practical alternative that approximates targeted effects without global information, by randomly selecting nodes and then vaccinating one of their neighbors. This method leverages the fact that neighbors of random nodes are more likely to be high-degree, achieving near-optimal protection; in scale-free networks with degree exponent between 2 and 3, the critical immunization fraction is approximately 0.25, a dramatic improvement over the for random immunization. The strategy's efficiency stems from a modified percolation threshold, where the probability of immunizing a node of degree scales with , yielding in the large-network limit. Ring vaccination, inspired by contact-tracing protocols, immunizes the immediate contacts of identified infected individuals to contain local outbreaks. Modeled as a mixed bond-node percolation process on SIR dynamics, it proves effective when tracing efficiency is high, halting epidemics by vaccinating a ring around cases; optimal allocation minimizes the giant outbreak size, with success depending on the fraction of traced contacts vaccinated, often requiring less than 20% coverage in clustered networks if tracing covers over 80% of edges. This strategy excels in reactive scenarios, complementing preventive measures like targeted immunization. Key metrics for evaluating these strategies include the critical immunization fraction , the minimum proportion of nodes that must be immunized to prevent a giant connected component or epidemic outbreak. In Erdős–Rényi random graphs, (where is the mean degree times transmission probability), typically around 0.5–0.8 for realistic epidemics, allowing robust protection with moderate effort. In contrast, scale-free networks exhibit under random immunization due to persistent hubs, but targeted and acquaintance methods reduce to 0.1–0.3, highlighting the topology-dependent vulnerability and the superiority of structure-aware approaches.[95]| Strategy | Critical Fraction in Scale-Free Networks | Critical Fraction in Random Graphs | Key Advantage | Citation |
|---|---|---|---|---|
| Random | Simple implementation | |||
| Targeted (Degree) | (for ) | Lower than random, but less studied | Maximizes hub disruption | [95] |
| Acquaintance | Comparable to targeted | No global knowledge needed | ||
| Ring | <0.2 (with high tracing) | Effective locally, scales with clusters | Reactive containment |